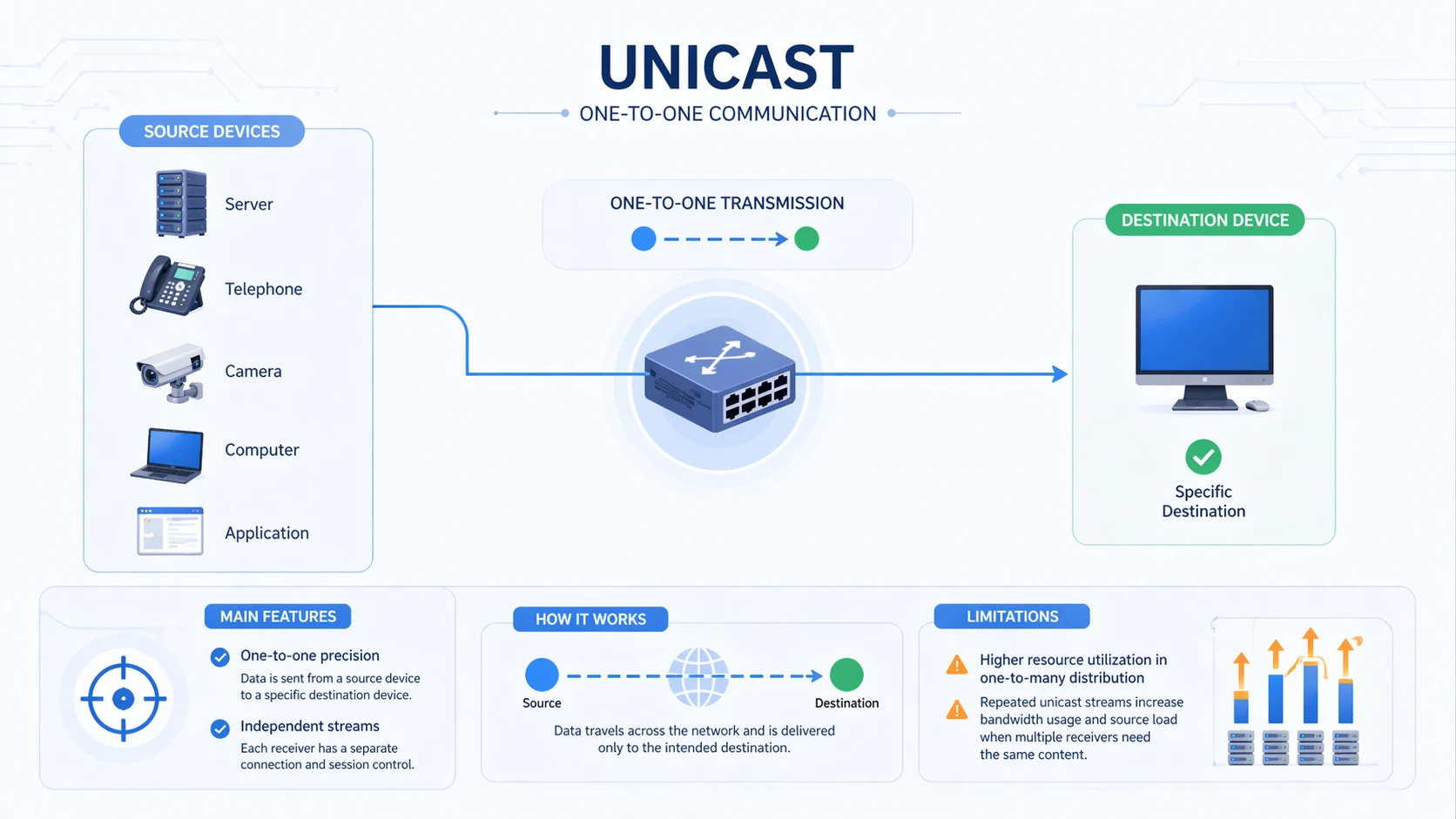
Unicast is a communication method in which data is sent from one source device to one specific destination device. In simple terms, it is a one-to-one transmission model. When a server, phone, camera, computer, or application sends information using unicast, that information is directed to a single receiving endpoint rather than to every device on the network or to a group of recipients. This makes unicast one of the most common and fundamental traffic delivery methods in IP networking.
Most everyday network communication depends on unicast. A web page loaded in a browser, a file downloaded from a server, a VoIP call between two endpoints, a login session to a cloud platform, or a remote management connection to a network device are all common examples of unicast behavior. The data is intended for one receiver, and the network forwards it accordingly.
Because unicast is so common, it is often taken for granted. However, it is an important concept in network design, bandwidth planning, communication architecture, and application behavior. Understanding unicast helps explain how many modern digital services operate, why some traffic patterns scale well or poorly, and how network engineers choose between one-to-one, one-to-many, and group-based delivery models.
What Is Unicast?
Definition and Core Meaning
Unicast is a packet delivery model in which one sender transmits data to one receiver using a specific destination address. In IP networking, that usually means a packet is addressed to one unique host IP address, and routers or switches forward the traffic toward that single endpoint. The communication path is built around the idea that the transmission is intended for only one destination at a time.
The core meaning of unicast is exclusivity of delivery. The sender does not distribute the same packet simultaneously to every node on the network, nor to a subscribed group. Instead, it creates a distinct traffic flow for the intended receiver. If the same content must reach five separate users through unicast, the source or network generally creates five separate one-to-one streams rather than one shared stream for all five.
This is why unicast is often contrasted with broadcast and multicast. Broadcast aims at all devices within a broadcast domain. Multicast aims at a defined group of interested receivers. Unicast, by contrast, is targeted at one destination and is therefore the most direct and individually addressed communication model.
Unicast is the default language of most IP communication because so many network interactions are really one sender talking to one receiver.
Why It Matters in Networking
Unicast matters because it forms the basis of many routine and critical digital services. Most business applications, web sessions, cloud connections, voice calls, secure tunnels, management sessions, and enterprise transactions depend on the ability to move information precisely from one endpoint to another. Without unicast, many core network activities would not function in a practical way.
It also matters because the unicast model influences performance and scalability. One-to-one delivery is highly precise and easy to understand, but it can consume more bandwidth when the same content must be sent to many separate users. This is why engineers often evaluate whether a service should remain unicast or move toward multicast or broadcast-like distribution depending on the use case.
In short, unicast is both a basic communication model and an important design factor. It is foundational to how networks deliver controlled, destination-specific traffic across local and wide-area environments.
How Unicast Works
Source, Destination, and Addressed Delivery
Unicast works by using a specific destination address that identifies the intended receiver. A sender creates a packet, places the destination IP address in the appropriate header field, and sends the traffic into the network. Switches and routers examine the destination information and forward the packet toward the single device that owns that address.
At Layer 2, the local network still needs to deliver frames to the correct hardware destination, which may involve MAC address resolution. At Layer 3, routers make forwarding decisions based on IP addressing and routing tables. The end result is that the traffic follows a defined path toward one target rather than being distributed generally.
This one-destination model makes communication precise. The sender knows who the intended receiver is, and the network uses its normal forwarding intelligence to deliver the traffic only where it belongs. This is a key reason why unicast is well suited to most application sessions and device-to-device communications.
Session-Based Communication and Flow Control
Many unicast interactions are session-oriented. A user opens a website, a SIP endpoint starts a call, a monitoring system polls one device, or a client downloads a file from a server. In each case, the communication is logically tied to a specific sender-receiver relationship. Even if the session involves many packets, it remains a one-to-one flow.
This makes unicast highly compatible with transport controls, security policies, authentication, session management, and traffic accounting. Firewalls, session border devices, application servers, and monitoring tools often work well with unicast because the communication relationships are clear and individually traceable.
The same clarity also helps with troubleshooting. If a user cannot reach a service, the engineer can examine the one-to-one path, the source and destination addresses, the session state, and the relevant forwarding rules. This is often simpler than diagnosing a more distributed traffic model.
Unicast does not only deliver data to one receiver. It also creates a clear relationship between the sender, the receiver, and the network path between them.
Main Features of Unicast
One-to-One Precision
The most important feature of unicast is precision. Each traffic stream is intended for one receiving endpoint, which gives the sender and the network a highly specific communication target. This makes unicast ideal for services where the content, state, or response is unique to the user or device involved.
For example, a secure login session, an IP phone registration, a device management connection, or a file requested by one user should not be delivered broadly to other devices. Unicast ensures that the traffic remains tied to the intended destination rather than being shared or exposed more widely than necessary.
This precision also supports cleaner policy enforcement. Access control, QoS treatment, monitoring, encryption, and session tracking can all be applied more directly when the traffic relationship is explicitly one to one.
Independent Streams for Independent Receivers
Another defining feature is that each receiver generally gets its own stream. If the same application content is sent separately to multiple users by unicast, the source may need to generate multiple distinct one-to-one traffic flows. This is common in web browsing, individualized media sessions, and many cloud applications.
This approach provides flexibility because each stream can potentially be managed independently. Different users may receive content at different times, with different session parameters, and with different control states. However, this independence can also increase resource usage if large numbers of receivers need identical content at once.
This dual nature is important. Unicast offers strong control and personalization, but network planners must understand that large-scale one-to-many delivery through repeated unicast streams may create bandwidth or server load concerns.

Unicast Versus Broadcast and Multicast
How Unicast Differs From Broadcast
Broadcast sends traffic to all devices within a broadcast domain, whether those devices actually need the data or not. Unicast does not behave that way. It directs traffic only to the specific destination that the sender intends to reach. This makes unicast much more targeted and typically more efficient for ordinary application communication.
Broadcast is useful for certain network discovery and infrastructure tasks, but it is not suitable for most application-level communication because it creates unnecessary visibility and processing for devices that are not the real destination. Unicast avoids that problem by keeping the scope of delivery narrow and intentional.
This is why most business, internet, and application traffic is unicast rather than broadcast. Precision is usually more useful than broad indiscriminate delivery.
How Unicast Differs From Multicast
Multicast sits between unicast and broadcast. It sends traffic to a defined group of receivers that have joined a multicast group. Unicast does not use group membership. It sends one stream to one receiver. If ten receivers need the same data through unicast, ten separate streams may be required. With multicast, one group-oriented distribution pattern may serve them more efficiently.
This makes multicast attractive for certain forms of live media distribution, paging, network audio, or shared data delivery where many receivers need the same content at the same time. Unicast remains more common where the communication is individualized, interactive, or session-specific.
In practical network design, the choice among unicast, multicast, and broadcast depends on who needs the data, how many receivers are involved, and whether the content is unique or shared.
Unicast is best when the destination is specific. Multicast is useful when the same data must reach a defined group. Broadcast is reserved for cases where everyone in a local domain needs to hear the message.
Benefits of Unicast
Clear Delivery and Strong Session Control
One of the biggest benefits of unicast is clear and predictable delivery. The sender knows exactly which destination is being targeted, and the network forwards the traffic accordingly. This makes unicast well suited to applications that depend on authentication, privacy, transaction control, or user-specific state.
Strong session control is another major advantage. Because each communication flow is tied to one receiver, it is easier to apply user-specific rules, bandwidth management, security controls, and logging. This is valuable in enterprise networks, cloud services, VoIP sessions, industrial device management, and remote access environments.
The same clarity also supports better troubleshooting and accountability. If traffic does not arrive where expected, the path and session can be inspected as a direct one-to-one relationship rather than as a group or domain-wide event.
Compatibility With Common Applications and Infrastructure
Unicast also benefits from broad compatibility. Most applications, devices, servers, routers, firewalls, and network services are built with unicast as a normal operating assumption. This makes it easy to deploy across standard enterprise and internet-connected environments without requiring specialized multicast planning or unusual forwarding behavior.
Because unicast fits naturally with common session models, it also works well with encryption, access policies, NAT behavior, SIP sessions, and remote service delivery. Many digital services depend on individualized state, and unicast supports that pattern directly.
This broad compatibility is one reason unicast remains the dominant communication model across most IP-based systems even when other delivery models are also available.
Limitations of Unicast
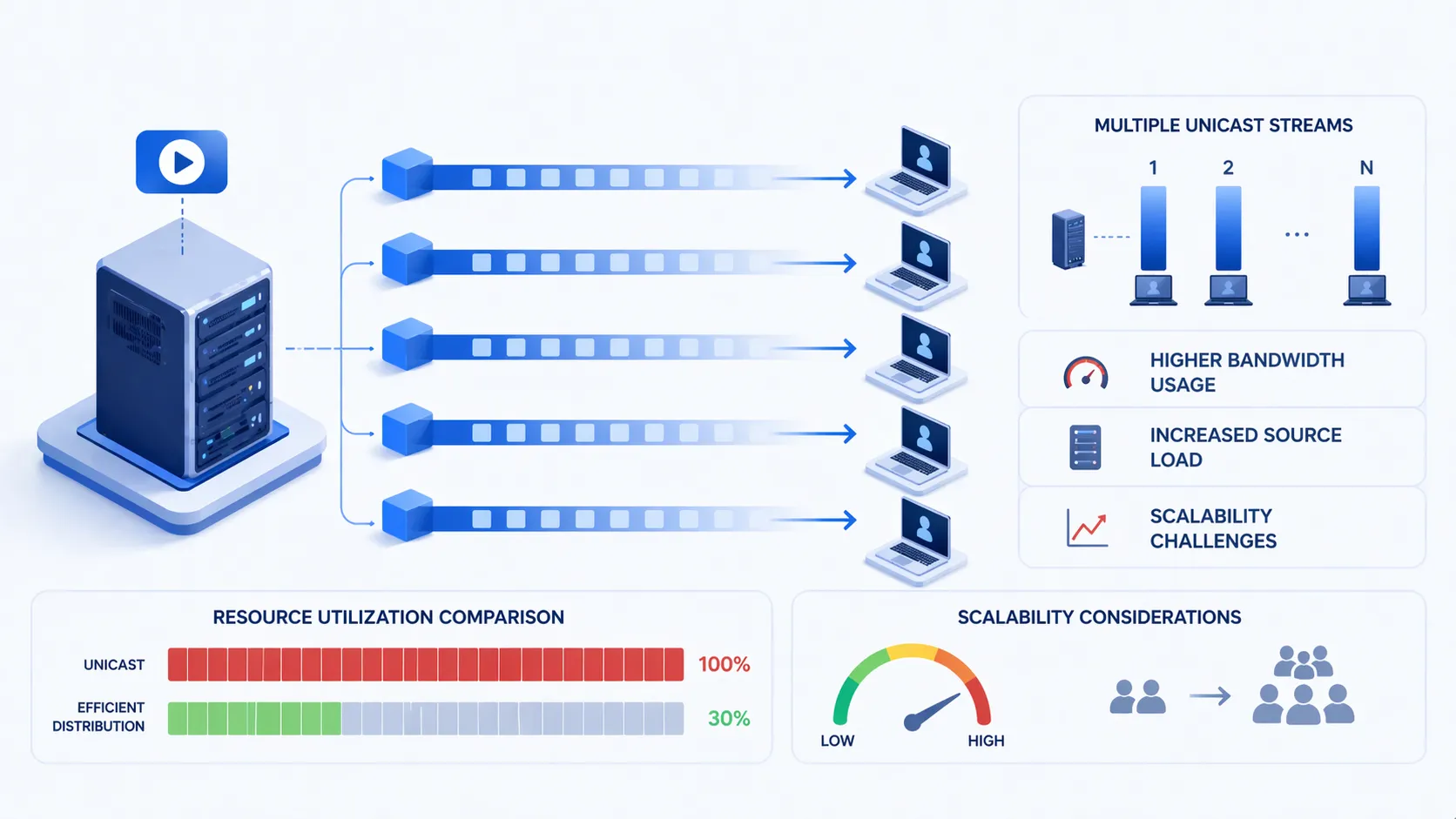
Higher Resource Use for One-to-Many Distribution
The main limitation of unicast appears when the same content must be delivered to many receivers at once. Because unicast usually creates separate streams for separate receivers, bandwidth and server load can grow significantly as the number of recipients increases. This can become inefficient in media distribution, large-scale streaming, or network-wide audio scenarios.
For example, if one live video source must be viewed by hundreds of devices, repeated unicast sessions may place heavy demand on the source and on the network. In such cases, multicast or a content-distribution approach may be more suitable.
This limitation does not reduce the value of unicast for ordinary application sessions. It simply means that engineers should recognize when one-to-one delivery is no longer the most efficient pattern for a growing number of receivers.
Scaling Considerations in Real-Time Services
Scaling can also be a concern in real-time communication or streaming systems. A unicast session works well for one call, one endpoint, or one user session. But when the same media must be sent to many endpoints simultaneously, repeated unicast streams can create pressure on bandwidth, forwarding devices, and source infrastructure.
This is especially relevant in network audio, surveillance distribution, live video services, or large soft-client environments. In these contexts, unicast remains useful, but planners may need to balance its advantages against resource consumption and look carefully at network capacity.
In short, unicast scales very naturally for individualized communication, but not always as efficiently for identical mass distribution.
Applications of Unicast
Web Access, Cloud Services, and Enterprise Networking
One of the most common applications of unicast is everyday web and cloud communication. When a user loads a website, authenticates to a platform, downloads a file, or accesses a SaaS application, the interaction is usually unicast. The server responds to one client, and the traffic remains tied to that one session.
Enterprise networking also depends heavily on unicast. User workstations connect to directory services, file servers, business applications, VPN gateways, and management systems through one-to-one communication. Remote administration sessions, database requests, secure application access, and system monitoring flows are all often unicast-based.
This makes unicast central to the normal operation of both internet services and internal business infrastructure. It is the standard delivery method for most user-specific and application-specific interactions.
VoIP, IP Telephony, and Industrial Communication Systems
Unicast is also widely used in VoIP and IP telephony. SIP signaling between endpoints and call servers is commonly unicast, and many media sessions are also carried as unicast streams between specific participants or between endpoints and media resources. Standard business calls, remote extensions, server registrations, and many intercom sessions all rely on one-to-one delivery.
In industrial communication systems, unicast is used for device management, control messaging, point-to-point intercom sessions, supervisory communications, and remote access to networked equipment. It fits especially well where communication is directed, controlled, and traceable rather than broadly distributed.
In solutions involving Becke Telcom IP phones, SIP terminals, gateways, intercom devices, and industrial communication platforms, unicast is naturally relevant because many of these devices depend on one-to-one signaling, registration, configuration, and direct session-based communication across the network.
Unicast in Modern Communication Design
Role in Secure and Personalized Services
Modern digital services increasingly depend on individualized sessions, authentication, encryption, and policy-driven access control. Unicast fits this environment well because it supports direct sender-to-receiver relationships rather than general or group-wide delivery. This helps make communication easier to secure, track, and personalize.
Whether the service is a secure web application, a management console, a VoIP session, or a remote device connection, the unicast model aligns naturally with the idea that one user or one device is interacting with one service endpoint at a given time. This makes unicast a strong fit for modern controlled communication design.
In this sense, unicast is not only a packet delivery method. It is also a practical architectural pattern for services built around individual identity, session state, and endpoint accountability.
Value in Hybrid and Converged Networks
In hybrid and converged networks, unicast remains highly valuable because many different service types still require precise destination control. Voice, signaling, management traffic, cloud access, industrial data exchange, and remote configuration sessions may all operate over the same infrastructure, yet still depend on clear one-to-one delivery.
This makes unicast a dependable foundation even in environments that also use multicast or broadcast for selected functions. The network does not choose one model for everything. Instead, it combines delivery models based on application need. Unicast often remains the dominant model because so many services are fundamentally individual in nature.
That is why unicast continues to be a core concept in enterprise IT, IP communications, industrial networking, and service design.
Even in networks that support many traffic models, unicast remains the backbone of most individualized communication.
How to Decide When Unicast Is the Right Choice
When Unicast Is the Better Fit
Unicast is the better fit when the communication is intended for one receiver, when the session is individualized, or when policy control, traceability, and destination precision matter most. It is ideal for user logins, web requests, point-to-point voice calls, device management, remote monitoring sessions, and controlled application communication.
It is also the better fit when each user needs a separate session state, separate security context, or separate application behavior. In those cases, group-based delivery would not match the service model as effectively as unicast.
This is why unicast is so widely used: many real digital interactions are naturally one to one.
When Another Model May Be Better
Another model may be better when the same data must reach many receivers simultaneously and efficiently. Multicast may be more suitable for live media, network audio, or shared content distribution where recipients belong to a known group. Broadcast may still be appropriate for limited local discovery or infrastructure functions.
The key question is whether the content is individualized or shared. If it is individualized, unicast usually makes sense. If it is identical and widely shared, repeated unicast streams may be less efficient than other models.
Good network design does not treat unicast as universally right or wrong. It treats it as the right model for many very common communication needs.
Conclusion
Unicast is a one-to-one communication method that sends data from one source to one specific destination. It is the most common traffic model in IP networking because so many digital services, including web access, cloud sessions, VoIP signaling, device management, and enterprise application traffic, depend on direct and individualized delivery.
Its main strengths are precision, clear session control, strong compatibility with modern infrastructure, and a natural fit for secure and user-specific services. Its main limitation appears when identical content must be delivered to many receivers, because repeated one-to-one streams can increase resource use.
For most modern networking and communication environments, however, unicast remains fundamental. It is one of the core traffic patterns that makes controlled, destination-specific digital communication possible across business, industrial, and service-provider systems.
FAQ
What is unicast in simple terms?
In simple terms, unicast means one sender sends data to one receiver. It is a one-to-one communication model used in most ordinary network sessions such as web browsing, file downloads, and many voice or application connections.
The traffic is directed to one specific destination rather than to all devices or to a group.
What is the difference between unicast and multicast?
Unicast sends traffic to one receiver, while multicast sends traffic to a defined group of receivers that have joined the multicast group. If the same content must reach many receivers, multicast can often be more bandwidth-efficient than repeated unicast streams.
Unicast is usually better for individual sessions, while multicast is more suitable for shared group delivery.
Where is unicast commonly used?
Unicast is commonly used in web access, cloud services, enterprise applications, VoIP signaling, point-to-point media sessions, device management, remote administration, and industrial communication systems.
It is the standard model for most digital interactions where one source is communicating with one intended destination.