Transmission Control Protocol, usually called TCP, is one of the foundational communication protocols of modern IP networks. It operates at the transport layer and is designed to move application data between endpoints in a reliable, ordered, and controlled way. When people open a website, download a file, send an email, establish a remote terminal session, or connect business software to a server, TCP is often the transport mechanism that keeps the exchange accurate and complete.
Unlike a simple best-effort delivery method, TCP does more than pass packets from one host to another. It establishes a logical connection, numbers data segments, confirms what has arrived, retransmits what was lost, regulates sending speed, and helps prevent a sender from overwhelming the receiver or the network. That combination of reliability, sequencing, and traffic control is the reason TCP remains a central protocol for applications where correctness matters more than minimal overhead.
TCP adds connection management, sequencing, acknowledgments, and traffic control on top of IP packet delivery.
What Is TCP?
TCP as a Transport-Layer Protocol
TCP is a transport-layer protocol in the Internet protocol suite. In practical terms, that means it sits above IP and below application protocols such as HTTP, HTTPS, SMTP, IMAP, FTP, database protocols, and many remote access services. IP handles addressing and routing across networks, while TCP handles end-to-end transport behavior between two communicating hosts.
This layering matters because application software usually does not want to manage packet loss, duplication, reordering, or rate adaptation on its own. TCP provides a standardized transport service that applications can use through sockets or equivalent operating-system interfaces. That service lets developers focus on the application message format and business logic while the transport layer handles delivery discipline.
TCP is often described as connection-oriented, but that phrase is sometimes misunderstood. It does not mean a fixed physical circuit exists between two systems. Instead, it means the sender and receiver create and maintain shared connection state so that data can be tracked, acknowledged, reordered if needed, and delivered to the application as a consistent byte stream.
Core Characteristics of TCP
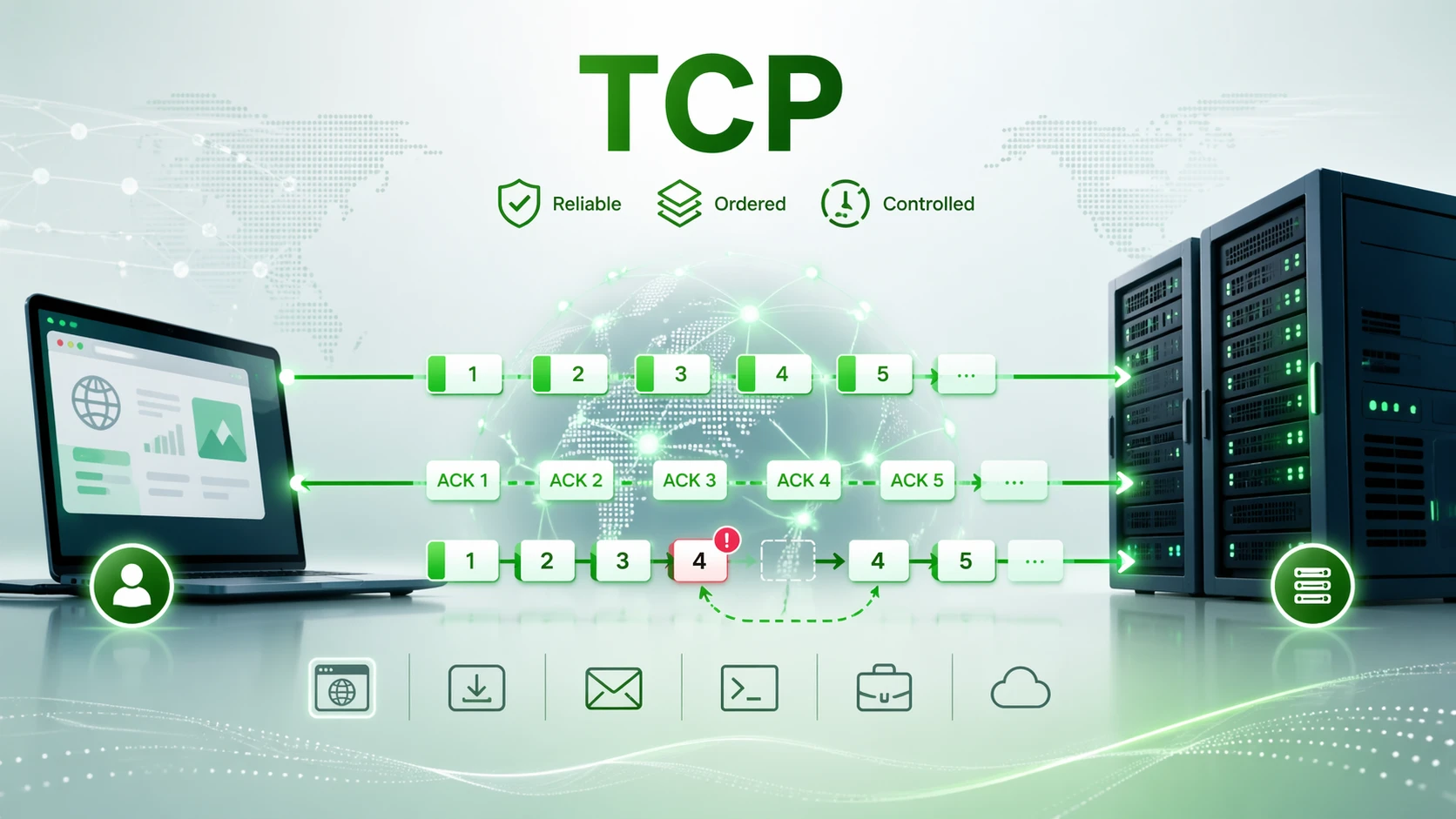
The most recognized characteristic of TCP is reliable delivery. Each side keeps track of sequence numbers, acknowledges data that has arrived, and detects missing information. If a segment is lost on the path, TCP can retransmit it. This helps the receiving application obtain a complete stream of data even when the underlying network is imperfect.
TCP also preserves order. Data may travel across the network in segments that do not arrive in exactly the same order they were sent, but TCP reassembles the stream before presenting it upward. For applications such as web transactions, file transfers, email retrieval, and database sessions, in-order delivery is usually essential because even small gaps or reordering can break the meaning of the data stream.
Another core trait is traffic regulation. TCP does not simply send as fast as possible forever. It applies flow control so the sender does not overrun the receiver, and it applies congestion control so the connection reacts to network conditions. These behaviors make TCP more cooperative and resilient than a bare send-and-forget transport approach.
TCP is not just a delivery method. It is a transport control system that combines connection state, sequencing, acknowledgment, retransmission, and rate adaptation into one standardized protocol behavior.
How TCP Works
Connection Establishment and the Three-Way Handshake
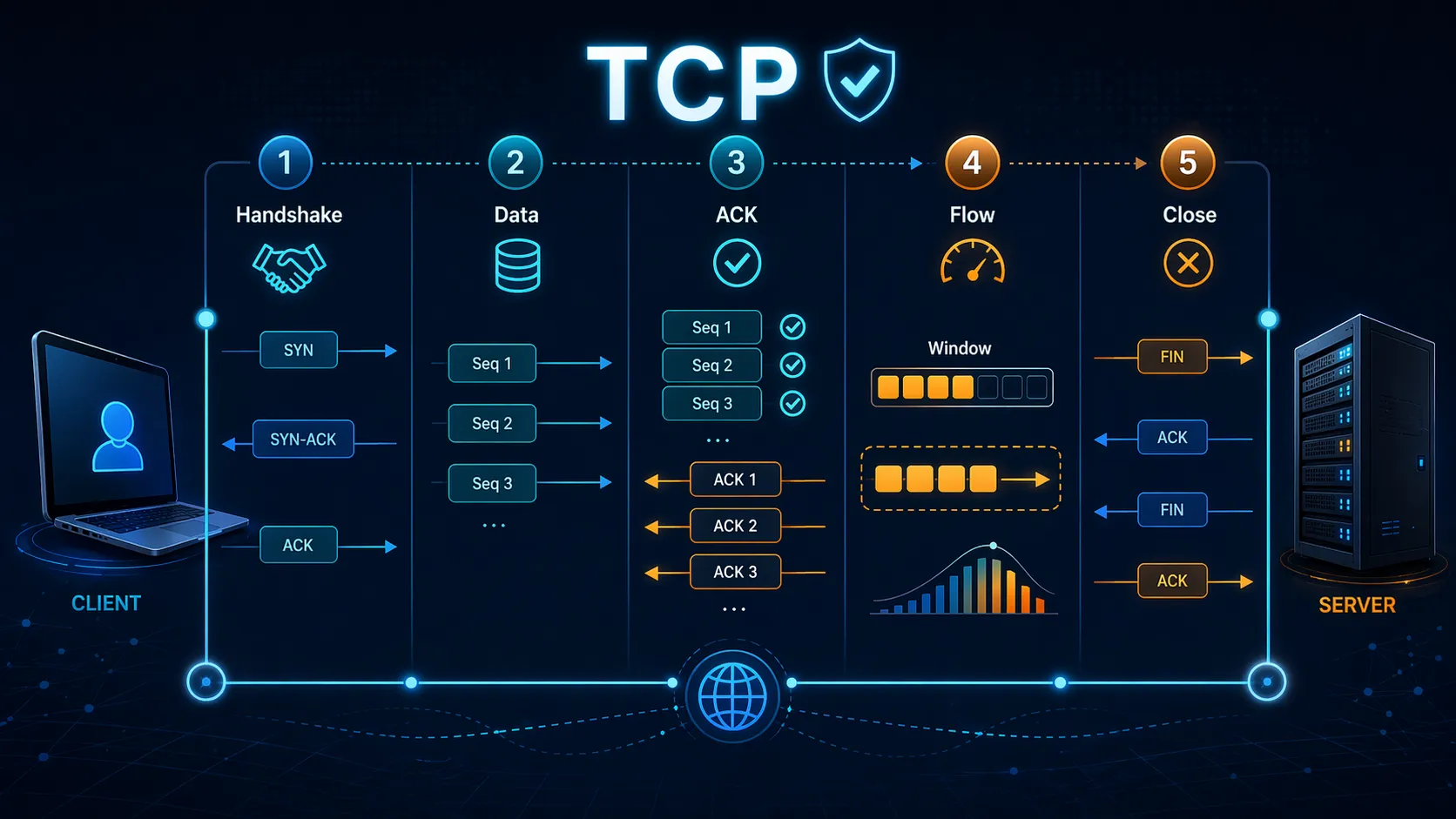
Before application data is exchanged, TCP normally establishes a connection using the well-known three-way handshake. A client begins by sending a synchronization request, commonly described as SYN. The server responds with SYN-ACK, which both acknowledges the initial request and announces its own sequence state. The client then completes the process with an ACK. After this exchange, both sides have enough shared state to start reliable data transfer.
The handshake is important because it does more than say hello. It confirms that both endpoints are reachable, negotiates initial sequence numbers, and prepares buffer and control state for the session. In many environments, additional mechanisms such as options for window scaling, selective acknowledgment support, and timestamps are also established during connection setup, improving efficiency on modern networks.
Because TCP is stateful, the connection setup phase introduces a small amount of delay compared with a connectionless transport. That overhead is a tradeoff: the application waits briefly at the start, but gains ordered and reliable delivery for the rest of the session.
Data Transfer, Sequencing, and Acknowledgments
Once the connection is established, the sender places application bytes into TCP segments and assigns sequence numbers to track their position in the stream. The receiver acknowledges the highest contiguous range of data it has received. If all segments arrive successfully, the acknowledgment process allows the sender to keep moving forward without resending previously delivered bytes.
If a segment is lost, delayed too long, or arrives out of order, the receiver's acknowledgments help the sender detect that the stream has a gap. The sender can then retransmit the missing data. This behavior is what allows TCP to hide many network impairments from the application layer. From the application's point of view, it still receives a coherent byte stream rather than a scattered set of packets.
TCP is stream-oriented rather than message-oriented. That means the protocol preserves byte order, not application message boundaries. Applications that need explicit message framing must define that logic themselves, which is why higher-level protocols often include delimiters, lengths, headers, or record structures above TCP.
TCP begins with connection setup and then maintains the stream through sequence numbers, acknowledgments, and retransmissions.
Flow Control and Congestion Control
Flow control and congestion control are related, but they solve different problems. Flow control protects the receiving host. A receiver advertises how much data it can currently accept, and the sender stays within that limit. This prevents a fast sender from overrunning a slower application or a smaller receive buffer.
Congestion control protects the network path. Even if the receiver can accept more data, the network in between may not be able to carry unlimited traffic without loss and delay. TCP therefore adjusts its sending behavior based on perceived congestion. In common descriptions, this includes mechanisms such as slow start, congestion avoidance, fast retransmit, and fast recovery. The exact behavior depends on the implementation and the congestion-control algorithm in use, but the goal is consistent: push throughput upward when the path is healthy and back off when congestion appears.
This adaptive behavior is one reason TCP is still trusted for large-scale data transport. It does not guarantee perfect fairness or maximum performance in every environment, but it gives applications a mature and interoperable transport model that responds to changing network conditions instead of assuming a stable path.
Connection Termination
When data transfer is complete, a TCP session is usually closed gracefully. One side sends a FIN to indicate it has finished sending data, and the other side acknowledges it. Because TCP is full-duplex, the reverse direction can continue briefly until that side also sends its own FIN and the exchange is acknowledged. This orderly shutdown helps both endpoints release connection state without silently discarding in-flight data.
In some fault or policy conditions, a connection may be reset rather than closed gracefully. A reset immediately tears down the session state, which can be useful when a port is unavailable, a process has failed, or a device intentionally rejects the connection. However, a reset is more abrupt and is not the normal form of clean application completion.
The practical value of TCP comes from its discipline: establish state, move bytes in order, confirm delivery, adapt to the path, and close the session cleanly.
Common Uses of TCP
Web Access, Secure Sessions, and Business Applications
TCP is widely used for web traffic and many application sessions that require integrity and order. Traditional HTTP uses TCP, and HTTPS commonly combines HTTP with TLS over TCP. Web portals, SaaS platforms, enterprise dashboards, APIs, and many identity services rely on this transport behavior because pages, records, authentication exchanges, and business transactions need dependable delivery.
Even when a modern platform presents real-time information in the browser, large parts of the underlying session may still depend on TCP-based protocols. Software updates, account logins, data synchronization, background downloads, and back-end service calls all benefit from a transport model that can retransmit lost data and preserve sequence across the connection.
For enterprise systems, this reliability is especially important when users expect accuracy rather than merely immediacy. If an inventory transaction, a medical record query, a financial report, or a configuration change arrives incomplete or out of order, the consequences can be much more serious than a small increase in latency.
File Transfer, Email, and Remote Administration
TCP is also central to file delivery and store-and-forward communication. Protocols for file transfer, email submission, email retrieval, and secure shell access have historically relied on TCP because they need complete and correct data reconstruction at the destination. A missing block in a file or a partially transmitted administrative command is usually unacceptable.
Remote administration is another strong example. When engineers log into servers, network devices, or industrial management systems, they typically want stable interactive sessions with reliable command delivery and ordered output. TCP supports that expectation by ensuring that typed commands and returned data are tracked and retransmitted if necessary.
In hybrid environments, TCP often carries synchronization traffic between on-premises systems and cloud services. Backup jobs, software repositories, ERP connections, customer portals, and management tools all commonly depend on its transport guarantees.
Databases, Middleware, and Industrial Systems
Many database engines and middleware platforms use TCP for client-server communication, replication, and service-to-service traffic. Database queries, result sets, and transaction responses are not tolerant of missing or reordered bytes. TCP's stream model and reliability mechanisms make it a natural fit for these workloads.
Industrial and operational systems also use TCP extensively where data integrity is more important than ultra-low-latency delivery. Device management, remote diagnostics, configuration access, historian synchronization, industrial server communication, and many control-system support applications rely on TCP-based transport even when the broader environment includes specialized field protocols as well.
That does not mean every industrial workload should use TCP. Time-critical control loops, multicast paging, or highly delay-sensitive media paths may use other transport choices. Still, for monitoring, management, reporting, and server-oriented application traffic, TCP remains a widely adopted foundation.
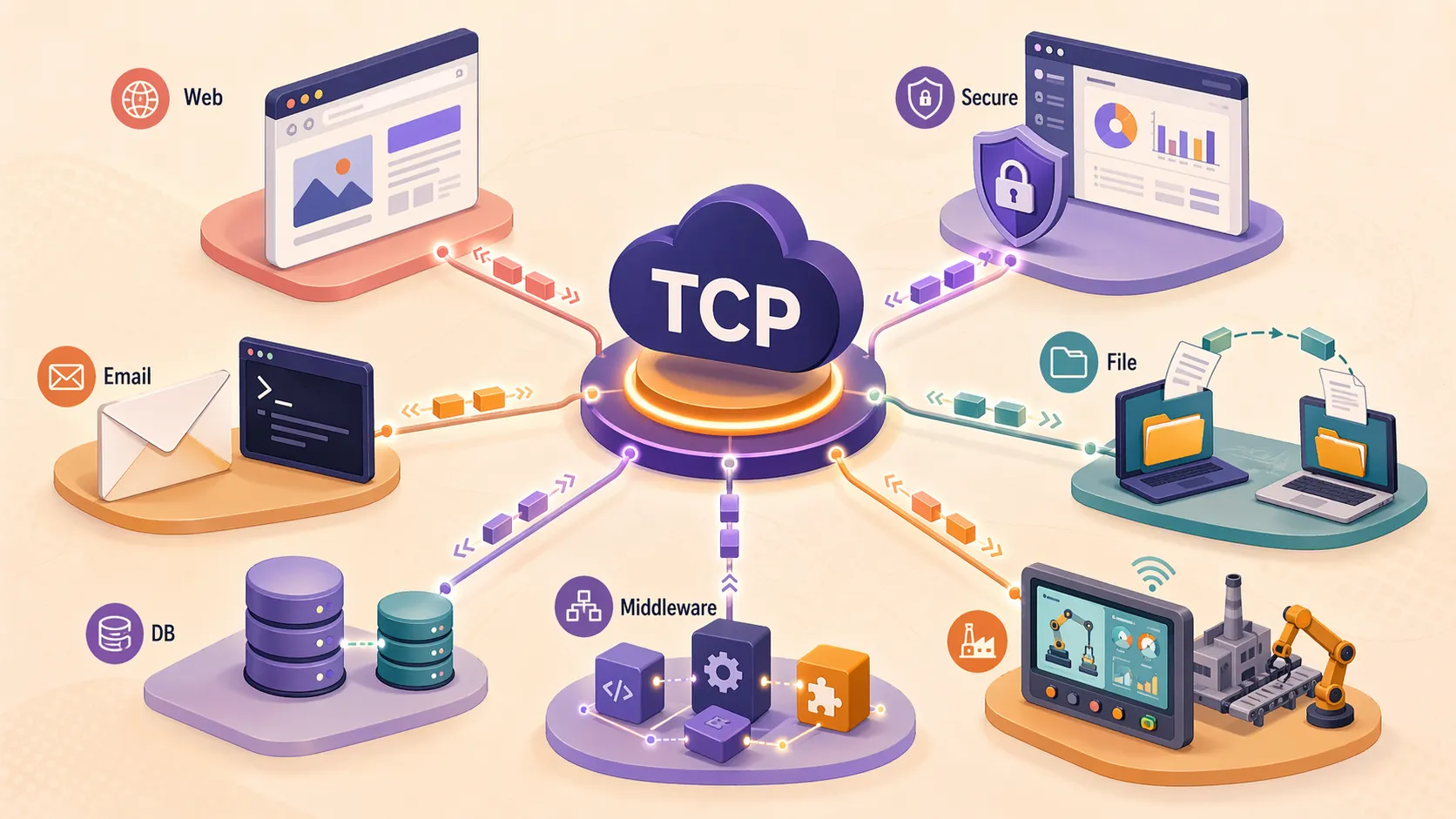
From websites and email to databases and industrial management platforms, TCP supports applications that depend on accurate transport.
Why Applications Choose TCP
Benefits of a Reliable Byte Stream
The biggest advantage of TCP is that applications receive a dependable transport service without implementing reliability from scratch. Developers do not need to create their own sequencing system, loss recovery logic, flow-control model, and connection lifecycle for every application. TCP provides mature, interoperable behavior that operating systems and network stacks already understand well.
Another important benefit is predictability. Because TCP has been deployed for decades, its behavior is widely supported across client devices, servers, firewalls, load balancers, and monitoring tools. This makes it easier to build services that can operate across mixed environments without demanding custom transport handling on every path.
TCP also pairs naturally with upper-layer security mechanisms such as TLS. That combination has become a standard foundation for secure websites, APIs, remote access tools, mail services, and many business applications that need both confidentiality and reliable transport.
Limitations and Tradeoffs
TCP is not always the best choice. Reliability, acknowledgments, retransmissions, and connection setup all add overhead. When an application is extremely sensitive to delay variation, or when late data is less useful than immediate partial data, TCP can become a poor fit. Real-time voice, interactive media, or certain broadcast and telemetry patterns may prefer transports that minimize latency and avoid head-of-line blocking.
TCP's ordered delivery model can also introduce waiting. If one segment is missing, later bytes may have to wait until the gap is repaired before the receiving application gets a fully ordered stream. For many transactional applications this is acceptable, but for some real-time experiences it can reduce responsiveness.
As a result, protocol selection should follow application goals. TCP is excellent when correctness, consistency, and compatibility are the priorities. It is less ideal when the main objective is the lowest possible latency with tolerance for some loss or reordering.
TCP Compared with UDP
Different Transport Philosophies
TCP and UDP are both transport-layer protocols, but they provide very different service models. TCP is connection-oriented and emphasizes reliability, ordering, retransmission, and transport control. UDP is connectionless and keeps transport behavior lighter, leaving many responsibilities to the application if they are needed at all.
That difference does not make one protocol universally better than the other. It reflects different design priorities. TCP is better aligned with applications such as web pages, file transfers, email, database access, and remote administration. UDP is often better aligned with scenarios such as DNS queries, certain streaming patterns, real-time media, multicast traffic, and custom low-latency application designs.
In practice, engineers choose between them by asking what matters most: complete ordered delivery, or minimal transport overhead and faster reaction to time-sensitive traffic. TCP answers the first need especially well.
Choosing the Right Fit
If an application cannot tolerate missing bytes, TCP is usually the safer starting point. That is why it remains common in line-of-business software, web infrastructure, cloud APIs, and inter-system synchronization. These environments benefit more from correctness and consistency than from shaving away a small amount of transport overhead.
If an application treats late data as useless, the calculation changes. A voice packet that arrives too late may be discarded rather than retransmitted, while a missing byte in a software package or account record is unacceptable. Understanding that distinction helps explain why TCP continues to dominate many application classes even as other transports are also used for specialized needs.
Applications of TCP Across Modern Networks
Cloud, Data Center, and Internet Services
Much of the modern Internet still depends on TCP somewhere in the service path. Public websites, internal web services, API gateways, storage access, management portals, email relays, backup repositories, and many cloud-native components all use TCP connections between clients, proxies, gateways, and servers.
Inside data centers, TCP is often the default transport for service access, database connectivity, administrative interfaces, and east-west traffic between application components. Even when a user sees only a simple browser session, multiple TCP-based exchanges may be occurring behind the scenes across web tiers, application tiers, and data layers.
The same is true for edge and branch environments. Retail systems, healthcare platforms, educational systems, remote offices, and industrial control support networks frequently depend on TCP for dependable application connectivity over LANs, WANs, VPNs, and private or public IP infrastructure.
Security, Monitoring, and Management Workloads
TCP is deeply embedded in security and management operations. SIEM platforms, log shipping, remote administration, patch delivery, asset management, authentication services, and centralized monitoring systems often depend on TCP because management data must arrive intact and in the right order to remain trustworthy and actionable.
Operational technology environments show a similar pattern. While control traffic may use specialized designs, the surrounding layers for management, analytics, alarming, historian collection, reporting, and remote engineering commonly depend on TCP-based services. This makes TCP important not only for user-facing applications but also for the infrastructure that keeps those applications visible, secure, and manageable.
Deployment Considerations for TCP-Based Services
Performance, Tuning, and Security Context
Using TCP successfully is not only about opening a port. Real performance depends on round-trip time, loss rate, window sizing, congestion-control behavior, buffer design, and application read-write patterns. A high-bandwidth path with high latency, for example, may need appropriate tuning and endpoint support to achieve efficient throughput.
Security design also matters. TCP itself provides transport reliability, not confidentiality or identity assurance. When encryption and endpoint authentication are required, TCP is commonly paired with TLS. Firewalls, load balancers, intrusion detection tools, and service meshes often inspect, proxy, or steer TCP-based sessions, so network policy and application design need to be aligned.
Finally, architects should remember that a successful TCP application depends on the full path, not only the protocol specification. Middleboxes, NAT devices, proxies, wireless links, and overloaded servers all influence how a TCP session behaves in production. Good design therefore considers application behavior, endpoint capacity, and network conditions together.
Conclusion
TCP remains one of the most important building blocks of IP communication because it provides a disciplined transport service for applications that require reliable and ordered delivery. By establishing a connection, sequencing bytes, acknowledging progress, retransmitting losses, and adapting to receiver and network conditions, TCP turns an imperfect packet network into a practical platform for dependable software communication.
Its strengths explain why it is still widely used across websites, secure sessions, email systems, file transfer, databases, management platforms, cloud services, and industrial support applications. Even as other transports serve specialized low-latency or media-heavy workloads, TCP continues to be the default choice whenever completeness, consistency, and interoperability are central requirements.
FAQ
What does TCP stand for?
TCP stands for Transmission Control Protocol. It is a transport-layer protocol used to provide reliable, ordered communication between endpoints across IP networks.
What is the main purpose of TCP?
The main purpose of TCP is to move application data reliably. It establishes connection state, tracks sequence numbers, acknowledges received data, retransmits missing segments, and controls sending behavior so the exchange remains accurate and manageable.
Is TCP connection-oriented?
Yes. TCP is connection-oriented because the two endpoints establish and maintain shared connection state before and during data transfer. This state enables reliable delivery, ordering, and traffic control across the session.
How does TCP differ from UDP?
TCP focuses on reliability, sequencing, acknowledgments, and congestion-aware transport behavior. UDP provides a lighter connectionless model with less transport overhead, which can be better for time-sensitive or loss-tolerant applications.
Does TCP provide encryption?
No. TCP provides transport reliability, not encryption. When confidentiality, integrity protection, and authenticated secure sessions are needed, TCP is commonly combined with TLS or another upper-layer security mechanism.
Where is TCP commonly used?
TCP is commonly used in web access, HTTPS sessions, email, file transfer, remote administration, database communication, cloud services, enterprise applications, monitoring systems, and many industrial management and support platforms.