A SIM card is one of the most fundamental components in mobile communication. It is the small secure module that helps identify a subscriber, support authentication, and enable a device to connect to a mobile network with the correct service profile. For most users, it is simply the card inserted into a phone, router, dongle, tracker, or gateway. In technical terms, however, it is a secure element that plays a critical role in subscriber identity, service authorization, and network access.
SIM cards have been part of mobile communication for decades, but their role has continued to evolve. What started as a removable card associated mainly with GSM phones now extends into UICC and USIM-based architectures, LTE and 5G authentication environments, IoT devices, industrial gateways, remote terminals, connected vehicles, and eSIM-enabled products. Even when the physical form factor becomes smaller or disappears into an embedded design, the underlying SIM function remains essential to how mobile operators identify and manage subscriber access.
That is why the SIM card is more than a storage chip for a phone number. It is part of the security and service architecture of the mobile network. It helps bind the user, device session, and operator environment together in a controlled way. Whether the endpoint is a consumer smartphone or an industrial communication gateway deployed in the field, the SIM function remains central to cellular connectivity.

SIM cards provide subscriber identity and secure network access across mobile communication systems.
What Is a SIM Card?
Basic definition
A SIM card is a secure subscriber module used in mobile communication systems to store identity-related and security-related information needed for network access. The term SIM originally refers to Subscriber Identity Module. In common usage, people use “SIM card” to describe the removable chip card placed into a phone, router, tablet, modem, or industrial terminal so that it can access a mobile operator’s network.
In modern technical language, the physical card is often better described as a UICC, or Universal Integrated Circuit Card, while the subscriber application on it may be a SIM, USIM, or other application depending on the network generation and service environment. Even so, “SIM card” remains the dominant everyday term across consumer, enterprise, and industrial discussions.
Why it exists
The SIM exists because a cellular network needs a secure way to identify a subscriber and verify that the device session is allowed to use the network. Without this secure identity layer, the operator would have a much harder time controlling access, assigning services, protecting subscriber credentials, and billing correctly. The SIM therefore serves both a user-side role and a network-side role.
From the user perspective, it makes the subscription portable. From the operator perspective, it creates a controlled and secure method for identifying the subscriber and applying the right service profile. This is one reason SIM-based cellular systems became so scalable across global mobile networks.
A SIM card is not just a card that stores a phone number. It is a secure subscriber identity and authentication element inside the larger mobile network architecture.
Core Features of a SIM Card
Subscriber identity storage
One of the most important functions of a SIM card is storing identity information associated with the subscription. A well-known example is the IMSI, or International Mobile Subscriber Identity, which helps the network recognize the subscriber. The SIM may also store other operator and service-related data used during device registration, roaming, and network selection.
This identity function is essential because the mobile network must distinguish one subscriber from another in a secure and standardized way. It is not enough for the device itself to exist on the network. The subscriber context must also be recognized and authorized.
Authentication support
Another critical feature is support for authentication and security procedures. The SIM environment helps the network verify that the subscriber is legitimate without exposing key security material in a simple or unsafe way. This process is part of how mobile systems protect access and establish trust between the subscriber side and the network side.
In practical deployment terms, this means the SIM plays a role in enabling secure attach and registration procedures rather than behaving like ordinary passive memory. Its value lies in secure identification and authentication, not just in data storage.
Service portability
SIM cards also support service portability. In traditional removable card usage, a subscriber can move the SIM from one compatible device to another and carry the subscription with them. This made mobile service far more flexible because the subscription identity was separated from the handset itself.
That portability became one of the defining strengths of SIM-based mobile systems and remains conceptually important even as embedded and remotely provisioned SIM models continue to grow.
Operator profile and service information
A SIM card may also store network-related parameters, application data, and service information used by the device and operator environment. Depending on the technology generation and service model, this can include data related to subscriber identity, authentication context, preferred network behavior, application support, or operator-specific functions.
This helps the device behave correctly when joining the network and can support a more consistent service experience across different devices and deployments.
Physical and logical security
SIM cards are built as secure elements rather than simple commodity memory cards. Their design reflects the need to protect sensitive subscriber and authentication data from unauthorized extraction or misuse. This is why the SIM function has remained central even as mobile architectures evolved from GSM to 3G, 4G, and 5G environments.
For industrial and enterprise deployments, this security role is especially important because remote assets, routers, IoT devices, and field gateways often depend on SIM-based trust for long-term unattended connectivity.
SIM Card, UICC, USIM, and eSIM: What Is the Difference?
SIM and UICC
In older and everyday language, people say SIM card to refer to the whole card. In more formal technical language, the physical smart card platform is often the UICC. The UICC is the card environment that can host one or more applications, including the subscriber application used for mobile network access. This distinction matters in standards discussions, but in product marketing and everyday conversation, the shorter term “SIM card” is still far more common.
For practical purposes, most users do not need to separate the terms unless they are working on telecom architecture, device certification, or deep technical documentation.
SIM and USIM
The term SIM is historically tied to earlier GSM-style subscriber modules, while USIM refers to the application model more commonly associated with 3G and later systems. In many modern mobile devices, what people casually call a SIM card is actually a UICC hosting a USIM application for advanced network generations. Even so, the broader market still says “SIM” because it remains the most recognizable label.
This is why a product datasheet may say “SIM slot,” even though the underlying platform supports much more than the earliest SIM concept.
SIM and eSIM
eSIM does not eliminate the SIM function. Instead, it changes how that function is packaged and provisioned. Rather than relying on a removable plastic card, eSIM uses an embedded secure element with remotely provisioned operator profiles based on GSMA frameworks. In other words, the subscriber identity role remains, but the deployment model becomes more flexible for modern devices, especially in tightly integrated consumer products and IoT systems.
This evolution is particularly important in connected devices where remote management, sealed hardware design, or large-scale field deployment makes removable cards less convenient.
In simple terms, SIM is the familiar user term, UICC is the broader card platform term, USIM is a modern subscriber application concept, and eSIM is an embedded and remotely provisioned deployment model.
How a SIM Card Fits into Mobile Network Architecture
The device side
On the device side, the SIM card works together with the handset, modem, router, baseband processor, or communication module. When the device starts up or attempts network access, it communicates with the SIM environment to obtain the identity and security-related information needed for registration and authentication procedures. The SIM does not by itself create connectivity. It supports the device in presenting a valid subscriber identity to the network.
This means the SIM should be understood as part of a device-network interaction chain rather than as an isolated component. The radio module, protocol stack, device firmware, and SIM application all contribute to successful network access.
The radio access side
Once the device has subscriber credentials available through the SIM environment, it attempts to connect through the radio access network. Depending on the generation, this may involve GSM, UMTS, LTE, or 5G radio access technologies. The SIM itself is not the radio. It does not transmit signals over the air. Instead, it enables the subscriber side of the process that allows the radio-capable device to request access in a recognized and authorized way.
This distinction is important because many people assume the SIM alone provides network service. In reality, the SIM supports identity and security, while the modem and radio interface handle the actual access over the cellular air interface.
The core network side
On the operator side, the mobile core network uses subscriber databases and authentication functions to determine whether the subscriber should be allowed onto the network and which services should be applied. In legacy and evolving architectures, this may involve entities such as the HLR, AuC, HSS, or newer 5G subscriber and authentication functions. The network compares or processes the subscriber identity and security information in coordination with the SIM-related credentials.
As a result, the SIM becomes part of a larger trust chain spanning the device, the access network, and the operator’s core systems. This is one reason SIM architecture is so important for mobile security and service control.
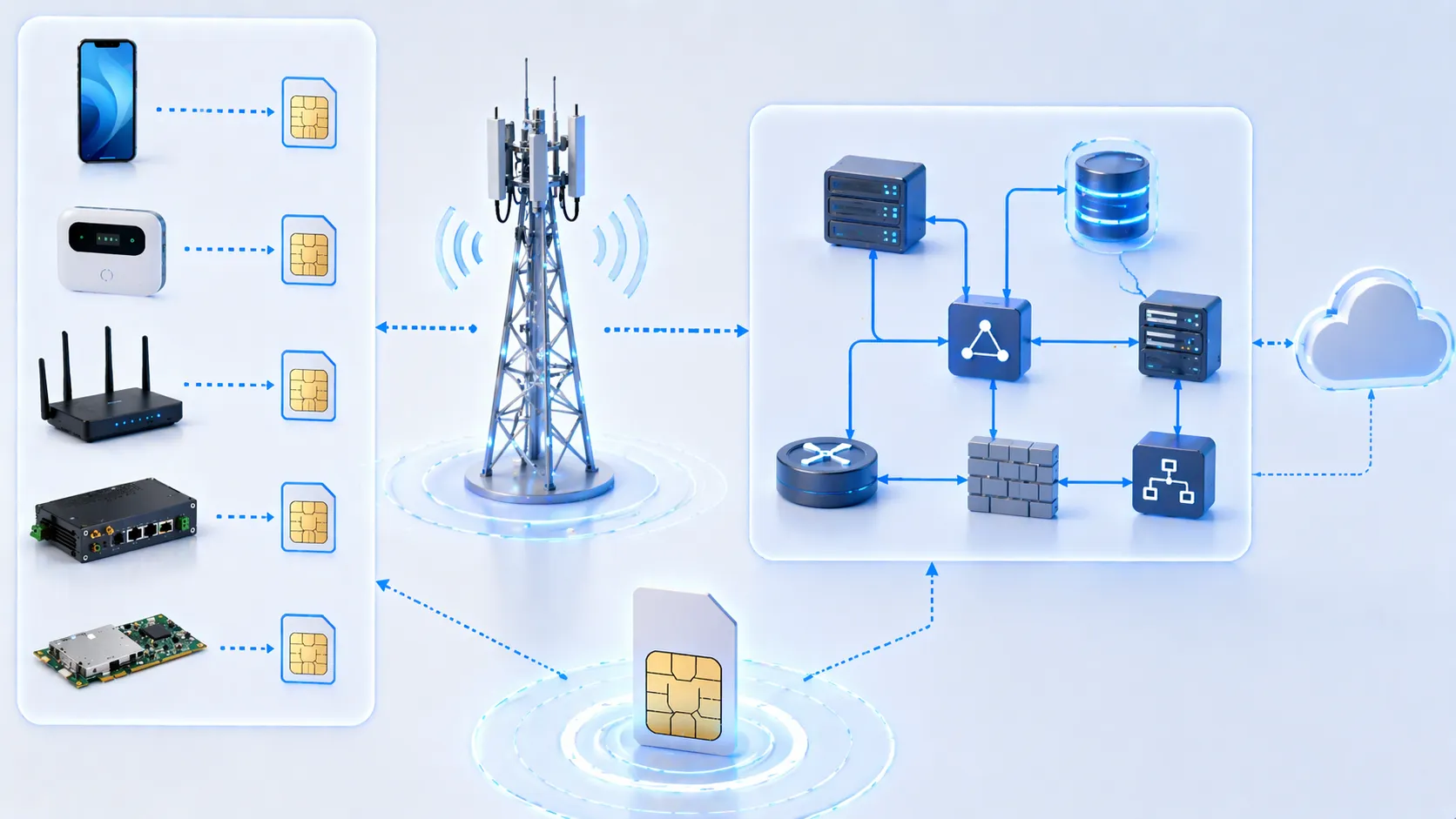
The SIM function sits within a broader architecture linking the device, radio access network, and core subscriber authentication systems.
Authentication and session establishment
During network access, the SIM supports the authentication process that helps prove the legitimacy of the subscription. When successful, the network can authorize service and allow the device session to proceed. This is one of the key reasons the SIM remains indispensable in cellular systems. It helps the operator avoid treating the device as an unauthenticated endpoint.
Although users may only notice that the phone has signal or that the router is online, behind that simple outcome is a structured identity and authentication workflow in which the SIM plays a central role.
Main SIM Card Form Factors
Standard, micro, and nano SIM
Over time, SIM cards have appeared in several physical form factors. Older devices often used larger standard SIM sizes, while later consumer devices moved to micro SIM and then nano SIM to save internal space. These changes reduced the surrounding plastic while preserving the essential contact function and subscriber role.
The shift in size reflects device design priorities rather than a change in the fundamental purpose of the SIM. Regardless of size, the card still supports subscriber identity and authentication functions.
Embedded SIM
Embedded SIM, or eSIM, takes the next step by moving away from a removable consumer card format. The secure SIM function is integrated into the device and operator profiles can be provisioned remotely. This is especially useful in wearables, IoT hardware, industrial equipment, connected vehicles, and sealed devices that are not convenient to open for manual SIM replacement.
For many industrial deployments, eSIM also supports more efficient lifecycle management because operator profiles can be changed or updated without physically replacing a card in the field.
Technical Capabilities That Matter in Practice
PIN and local user protection
SIM cards can support local access-control features such as PIN-based protection. This helps reduce casual misuse if the card or device is stolen, although the broader security value of the SIM comes mainly from its role in network authentication and protected subscriber functions.
In operational use, this local protection layer is only one part of the overall security model, but it remains familiar to end users and administrators.
Roaming support
SIM architecture also supports roaming behavior in mobile networks. Because subscriber identity is managed in a standardized operator framework, the subscriber can often access partner networks when traveling outside the home network’s direct coverage. The exact experience depends on operator agreements, device support, and service policy, but the SIM remains part of the identity chain that makes roaming possible.
This is one reason SIM-based mobile networks became so powerful globally. They allowed standardized subscriber identity to travel across network boundaries in a controlled way.
Application support and lifecycle flexibility
Depending on platform and operator design, SIM environments may support application logic, profile management, operator-specific service behavior, or remote lifecycle operations. In eSIM and IoT contexts, this becomes especially important because connectivity often needs to be managed over time rather than only at the point of sale.
For enterprises deploying thousands of devices, lifecycle flexibility can matter as much as basic connectivity. The SIM environment is therefore part of long-term operational strategy, not just first-day activation.
Common Applications of SIM Cards
Consumer smartphones and tablets
The most familiar application is consumer mobile devices such as smartphones and tablets. In these products, the SIM provides the subscriber identity and supports mobile voice, messaging, and data services. Users often think of it mainly as the item that activates the carrier line, but underneath that simple experience is the broader identity and security function that enables operator service.
Even in premium consumer devices moving toward eSIM, the same essential subscriber role still exists.
Wireless routers and mobile broadband equipment
SIM cards are widely used in 4G and 5G routers, CPE devices, dongles, and industrial gateways. In these products, the SIM allows the equipment to connect to the cellular network for broadband access, backup connectivity, branch networking, remote monitoring, or temporary deployment scenarios.
This is especially useful where wired infrastructure is unavailable, delayed, too costly, or insufficiently flexible for the application.
IoT devices and industrial equipment
Many IoT sensors, trackers, telemetry terminals, alarm panels, industrial gateways, vending systems, utility devices, and remote controllers depend on SIM-based or eSIM-based connectivity. These deployments often value wide-area wireless access, centralized fleet management, and secure subscriber identity more than consumer-style voice service.
In industrial environments, the SIM function helps provide persistent cellular connectivity across remote and distributed assets that may operate unattended for long periods.

SIM-based connectivity is used across consumer devices, routers, industrial gateways, trackers, and IoT endpoints.
Connected vehicles and transport systems
SIM and eSIM technologies are also important in connected cars, fleet systems, telematics devices, transport monitoring platforms, and onboard communication units. In these cases, the subscriber module helps enable remote diagnostics, data services, location-aware applications, and operator-managed connectivity across large geographic areas.
This is one of the clearest examples of how the SIM has evolved beyond traditional handset use into a broader machine connectivity role.
Remote communication and failover infrastructure
Many organizations use SIM-based cellular modules for backup links, remote site access, field communications, pop-up networks, and resilient communication design. Routers and gateways with SIM slots can provide failover WAN connectivity or primary access where fixed broadband is unavailable. This makes SIM support relevant not only to mobile users but also to enterprise and industrial communication architecture.
In these deployments, the SIM is part of business continuity and operational resilience, not just personal mobile service.
Advantages of SIM-Based Connectivity
Portable subscriber identity
One of the major advantages of the SIM model is that the subscription identity is separated from the device hardware. This allows flexibility in deployment, replacement, maintenance, and service migration. A subscriber or organization can move the identity from one supported device to another more easily than in a hardware-locked approach.
This concept remains valuable even in embedded models, because it shaped the broader philosophy of portable operator identity.
Secure operator-managed access
SIM-based networks provide a secure and operator-managed way to authenticate subscribers and control service access. This gives mobile systems a structured trust model that works at large scale across many device types and geographic regions.
For both operators and customers, this helps create a more controlled connectivity environment than an unmanaged identity model would allow.
Scalable for consumer and machine deployments
Another advantage is scalability. The same broad SIM-based identity model can support individual phone users, enterprise fleets, industrial terminals, transport systems, and massive IoT deployment strategies. That scalability is one reason SIM-centered cellular architecture remains foundational even as device types continue to diversify.
It supports both familiar personal communication and modern machine-to-machine service models within a common subscriber framework.
Things to Consider When Choosing a SIM Strategy
Physical SIM or eSIM
One of the first decisions is whether the deployment should use removable SIMs or eSIM architecture. Physical SIMs are easy to understand and replace manually, while eSIM can be better for sealed devices, large fleets, remote provisioning, or lifecycle flexibility. The right choice depends on how the device will be deployed, serviced, and managed over time.
For industrial and OEM projects, this choice can affect manufacturing design, field maintenance, logistics, and operator provisioning workflows.
Consumer, enterprise, or IoT profile needs
Different applications need different service models. A smartphone subscriber profile is not always the same as an industrial IoT connectivity profile. Data plans, roaming behavior, management interfaces, provisioning models, and lifecycle expectations may vary widely depending on the application. The SIM strategy should therefore match the actual business and technical use case.
What works well for a personal handset may not be the best fit for a utility sensor, a transport gateway, or a remote industrial terminal.
Network compatibility and deployment region
It is also important to consider network generation support, operator compatibility, roaming needs, and regional deployment requirements. A SIM strategy should be aligned with the modem, the radio bands, the device certification path, and the target countries or operator partners. Subscriber identity alone is not enough if the surrounding cellular design is incomplete.
Successful deployment comes from matching the SIM approach with the full communication architecture rather than treating the card as an isolated purchase item.
Choosing a SIM solution is not just about card size. It is about subscriber management, security, operator fit, device design, lifecycle control, and long-term connectivity strategy.
Conclusion
A SIM card is a secure subscriber identity and authentication element that enables devices to access mobile networks in a controlled and scalable way. Although the term often sounds simple, the SIM plays a deep role in cellular architecture by supporting identity storage, authentication, operator-managed service access, and connectivity portability across many kinds of devices.
From smartphones and tablets to routers, industrial gateways, IoT terminals, and connected vehicles, SIM-based connectivity remains central to modern mobile communication. Even as the industry moves toward UICC, USIM, and eSIM-based models, the essential subscriber function remains the same: to provide a trusted link between the device and the operator’s mobile network environment.
In short, the SIM card is not just a removable chip. It is a foundational part of the way mobile networks identify users, secure access, and deliver services across consumer, enterprise, and industrial applications.
FAQ
What does SIM stand for?
SIM stands for Subscriber Identity Module. In everyday use, it refers to the card or embedded subscriber module that helps a device connect to a mobile network.
Is a SIM card the same as a UICC?
Not exactly. In more formal technical language, the UICC is the broader smart card platform, while SIM or USIM can be applications on that platform. In everyday language, people often still say SIM card for the whole thing.
What does a SIM card store?
A SIM card stores subscriber-related and security-related information used for network identification and authentication. It may also hold operator and service-related data depending on the design.
Can a device work on a mobile network without a SIM card?
In most conventional cellular subscription models, a SIM or equivalent subscriber function is needed for normal operator-managed network access. Some special cases exist, but SIM-based identity remains the standard approach.
What is the difference between a physical SIM and an eSIM?
A physical SIM is a removable card, while an eSIM is an embedded secure SIM function that supports remote profile provisioning. Both serve the subscriber identity role, but they differ in packaging and management model.
Why is a SIM card important in IoT and industrial devices?
Because it helps provide secure cellular connectivity, subscriber management, and operator-controlled network access for remote devices such as gateways, trackers, sensors, routers, and field equipment.
Does a SIM card provide signal by itself?
No. The SIM supports subscriber identity and authentication, but the device’s modem and radio hardware handle the actual wireless communication with the network.