Secure Real-Time Transport Protocol, commonly abbreviated as SRTP, is a security profile for protecting real-time media streams such as voice, video, and audio communication. It is mainly used to secure RTP media traffic in systems such as VoIP calls, video conferencing, WebRTC sessions, SIP communication, contact centers, telemedicine platforms, online meetings, and real-time collaboration services.
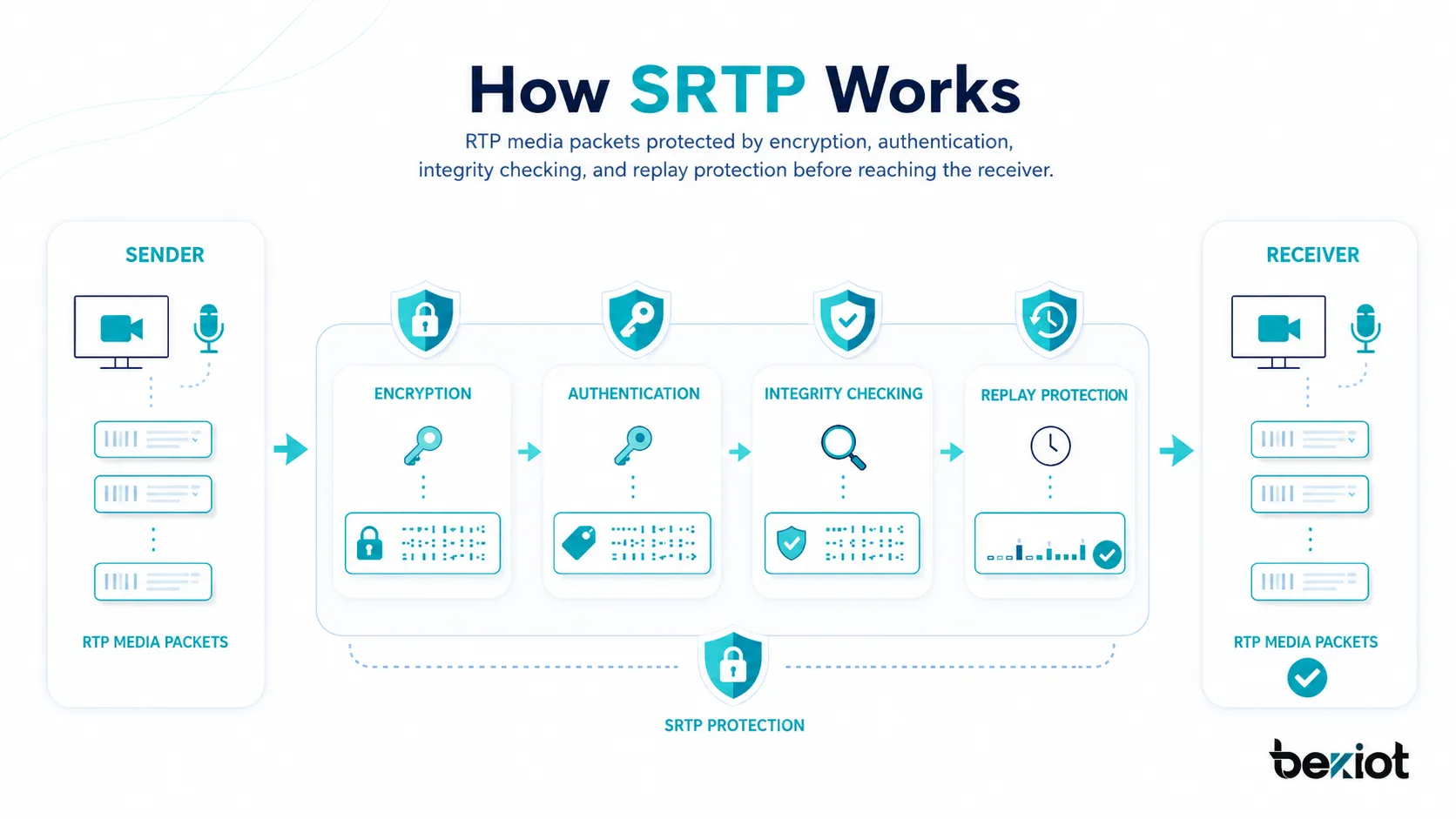
RTP is widely used to carry real-time audio and video, but ordinary RTP does not provide strong protection by itself. If media is sent as plain RTP across an untrusted network, attackers may be able to capture packets, listen to audio, inspect video traffic, inject packets, or replay old packets. SRTP addresses these risks by adding encryption, message authentication, integrity protection, and replay protection to media streams.
In modern communication systems, SRTP is an important part of secure voice and video architecture. It protects the media path, while other protocols such as TLS may protect signaling. This separation is important because a call can be properly signaled but still expose voice or video if the media stream is not secured. SRTP helps ensure that the content of real-time communication remains protected during transmission.
What Is SRTP?
Definition and Core Meaning
SRTP is a secure version of RTP designed for real-time communication. It keeps the timing and delivery advantages of RTP while adding security services to protect the media stream. These services can include confidentiality, message authentication, integrity checking, and replay protection.
In simple terms, SRTP protects the actual voice or video packets that travel between communication endpoints. When two people join a VoIP call, video meeting, WebRTC session, or secure conferencing service, SRTP can protect the media content so that unauthorized parties cannot easily listen, view, modify, or replay the stream.
The core meaning of SRTP is secure media transport. It does not replace SIP, WebRTC signaling, IP PBX routing, or conferencing control logic. Instead, it protects the real-time media packets that those systems create and exchange.
SRTP is used to secure the media path of real-time communication, protecting voice and video packets as they travel across IP networks.
Why SRTP Matters
SRTP matters because real-time communication often carries sensitive information. Business calls may include contracts, customer records, account details, internal decisions, or operational instructions. Healthcare video sessions may include private medical information. Emergency communication may include location, response instructions, or incident details. Without media protection, this information may be exposed during transmission.
Plain RTP can be captured and analyzed if an attacker has access to the network path. In local networks, public Wi-Fi, shared infrastructure, cloud environments, carrier networks, or compromised segments, unencrypted media traffic can create privacy and security risks.
SRTP reduces these risks by protecting the media stream itself. Even if packets are captured, encryption and authentication make it much harder for unauthorized parties to understand or manipulate the communication content.

How SRTP Works
RTP Media Before Security
RTP is designed to transport real-time media such as audio and video. It includes information needed for media playback, such as sequence numbers, timestamps, and payload type. These fields help receiving systems reorder packets, manage timing, and play audio or video smoothly.
However, standard RTP does not encrypt the media payload. This means that if ordinary RTP packets are captured, the audio or video content may be exposed. RTP also does not provide strong protection against packet tampering or replay attacks by itself.
SRTP adds a security layer around RTP so that the media stream can remain suitable for real-time communication while gaining protection against common network threats.
Encryption of Media Payloads
One of the main functions of SRTP is encryption. Encryption protects the media payload so that unauthorized parties cannot easily decode the voice or video content. In a voice call, this means the spoken audio is protected. In a video session, this means the visual stream can be protected as well.
SRTP is designed to keep overhead low because real-time media is sensitive to delay. A security method that adds too much processing time, packet size, or retransmission complexity would harm call quality. SRTP is therefore designed for real-time environments where low latency and predictable packet handling are important.
Encryption protects confidentiality, but confidentiality alone is not enough. SRTP also supports authentication and replay protection to help verify that packets are genuine and fresh.
Message Authentication and Integrity
SRTP can include message authentication, which helps confirm that packets were created by a valid sender and were not modified in transit. This is important because an attacker might try to inject fake packets, alter media content, or interfere with communication.
Integrity protection helps the receiver detect whether a packet has been changed. If the authentication check fails, the packet can be rejected. This helps reduce the risk of malicious media manipulation or packet injection.
In secure communication, integrity is just as important as encryption. A private call is not enough if attackers can alter or inject media packets without detection.
Replay Protection
Replay protection helps prevent attackers from capturing valid media packets and sending them again later. In a voice or video session, replayed packets could create confusion, interfere with audio, or disrupt communication.
SRTP uses packet sequence information and replay protection logic to detect old or duplicated packets. If a packet appears to be a replay, the receiver can discard it.
This protection is especially useful in real-time communication because media packets must be accepted quickly, but the system still needs to reject suspicious repeated traffic.
Secure RTCP
RTP is commonly accompanied by RTCP, which carries control information about the media session, such as statistics, synchronization information, and quality feedback. SRTP has a related protection method for RTCP called SRTCP.
SRTCP helps protect control traffic associated with the media stream. This matters because RTCP data may reveal session behavior or be used to influence media quality reporting. Protecting both RTP and RTCP gives the communication session a more complete security model.
In a secure media architecture, both the media stream and the related control traffic should be considered.
SRTP Key Management
Why Keys Are Required
SRTP needs cryptographic keys to encrypt and authenticate media packets. Both sides of a communication session must have the correct keying material before protected media can be exchanged. Without proper key management, endpoints cannot decrypt or verify each other’s SRTP packets.
SRTP itself defines how media can be protected, but a communication system still needs a method to establish, exchange, or derive the keys used for that protection. This is why key management is an important part of SRTP deployment.
Poor key management can weaken the entire system. Even if SRTP is enabled, weak keys, exposed keys, reused keys, or insecure negotiation can create security risk.
DTLS-SRTP
DTLS-SRTP is a common method for establishing SRTP keys, especially in WebRTC environments. DTLS is used to negotiate keying material on the media path, and SRTP is then used to protect the real-time media stream.
This approach is useful because it does not depend only on out-of-band signaling to deliver media keys. It allows endpoints to negotiate security parameters directly in a way suitable for modern browser-based and real-time communication systems.
WebRTC systems commonly rely on DTLS-SRTP because browser-based voice and video communication requires strong default media protection and interoperable key establishment.
SDES and Other Keying Methods
Some SIP-based environments have used SDES, where SRTP keying information is carried in signaling. This approach may be simpler in certain controlled networks, but it requires signaling protection because keys exposed in signaling could compromise media security.
Other methods and architectures may use different key management techniques depending on platform design, device support, compliance requirements, and interoperability needs. The important point is that SRTP security depends not only on the media encryption algorithm but also on how keys are created, exchanged, stored, and protected.
When evaluating SRTP, administrators should check both media protection and key management. Enabling SRTP without secure signaling or proper key handling may create a false sense of security.
Main Features of SRTP
Media Confidentiality
Media confidentiality means that the audio or video payload is protected from unauthorized viewing or listening. This is one of the most important SRTP features because real-time communication often carries private, operational, or regulated information.
In a VoIP call, confidentiality helps protect spoken content. In a video conference, it helps protect visual communication. In a telemedicine session, it helps protect patient conversations. In a corporate meeting, it helps protect internal discussion.
Confidentiality is the feature most people associate with encrypted communication, but SRTP also provides additional protections needed for trustworthy media transport.
Low-Latency Security
SRTP is designed for real-time communication. Voice and video cannot tolerate long delays, heavy retransmission, or large processing overhead. SRTP provides security while keeping media delivery efficient enough for interactive communication.
This is different from file encryption or store-and-forward messaging, where delay may be less noticeable. In a live call, even small delays can affect conversation quality. SRTP is optimized for the timing requirements of real-time packet media.
Low-latency security makes SRTP suitable for voice calls, video meetings, live conferencing, dispatch sessions, and interactive collaboration.
Packet Authentication
Packet authentication helps verify that media packets are legitimate. This reduces the risk of unauthorized packet injection or tampering. In real-time communication, this is important because attackers may attempt to disturb a session by sending forged packets.
Authentication also helps the receiving endpoint make quick trust decisions. If a packet fails authentication, it can be discarded rather than played or processed.
This feature improves the reliability and security of the media stream.
Replay Protection
Replay protection helps detect old packets that are resent into the session. Without replay protection, captured packets could potentially be reused to disrupt the call or confuse media playback.
SRTP uses sequence-related logic to identify packets that should not be accepted again. This is important in packet networks where real-time media must be processed quickly.
Replay protection strengthens SRTP against a class of attacks that encryption alone does not fully address.
Compatibility with Real-Time Media Systems
SRTP is designed to work with RTP-based communication systems. This makes it practical for many existing VoIP, conferencing, and media platforms. Instead of replacing the entire media transport model, SRTP secures the RTP media stream.
This compatibility helps vendors and service providers add media security to systems that already use RTP. It also supports interoperability when endpoints, servers, and gateways are configured with compatible security parameters.
Compatibility is one reason SRTP remains important in modern communication systems.
Uses of SRTP
Secure VoIP Calls
SRTP is widely used to secure VoIP calls. In a SIP phone system, SIP may establish the call, while RTP carries the media. If RTP is not secured, the voice stream may be exposed. SRTP protects the voice packets.
This is important for businesses, call centers, healthcare providers, legal offices, financial organizations, government agencies, and any environment where phone conversations may contain sensitive information.
Secure VoIP design often combines SRTP for media with TLS or another secure method for signaling. Both signaling and media should be protected for a stronger security posture.
Video Conferencing
Video conferencing platforms can use SRTP to protect audio and video streams between participants, media servers, or conferencing bridges. This helps reduce the risk of unauthorized listening or viewing during online meetings.
Video communication usually carries more sensitive context than audio alone. Screen content, faces, room backgrounds, documents, and visual demonstrations may all be exposed if media is not protected.
SRTP helps conferencing systems provide secure real-time collaboration across public and private networks.
WebRTC Communication
WebRTC commonly uses SRTP to protect media streams in browser-based real-time communication. This includes web calling, video chat, telehealth platforms, customer support video, online education, remote interviews, and collaboration applications.
In WebRTC, SRTP is typically paired with DTLS-SRTP for key establishment. This provides a secure media path suitable for browser and application environments.
Because WebRTC is often used across the public internet, media encryption is especially important for privacy and trust.
Secure Contact Centers
Contact centers may use SRTP to protect conversations between customers, agents, supervisors, recording systems, and communication platforms. This is important when calls include account numbers, personal information, healthcare details, payment discussions, or support records.
SRTP can help protect the live media stream as it travels between endpoints and call platforms. It should be combined with secure recording storage, access controls, signaling protection, and compliance policies.
For regulated or customer-sensitive industries, SRTP can be part of a broader communication security strategy.
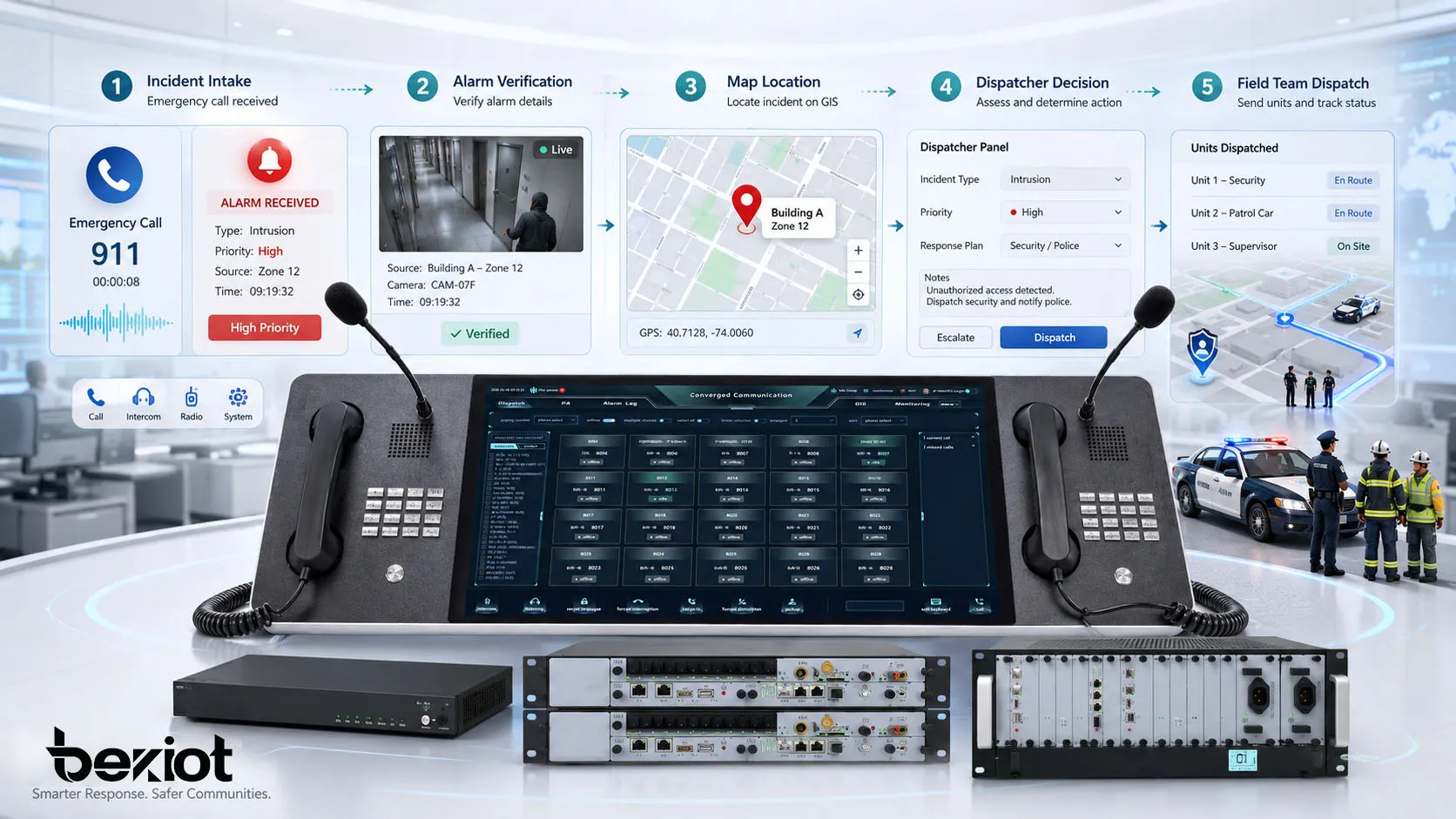
Emergency and Dispatch Communications
Emergency and dispatch communication systems may use SRTP to protect operational voice and video streams. Dispatch calls may include sensitive incident details, field response information, location data, or coordination instructions.
In these environments, communication must be both secure and reliable. SRTP helps protect the media stream while preserving real-time performance. Network quality, redundancy, priority handling, and endpoint reliability remain important.
Secure media transport can help protect command communication from interception or manipulation.
Benefits of SRTP
Improved Privacy
The most direct benefit of SRTP is improved privacy for real-time media. It helps prevent unauthorized parties from listening to voice calls or viewing video streams by encrypting the media payload.
This matters for organizations that discuss confidential business information, personal data, medical details, financial topics, legal matters, or operational instructions over voice and video systems.
SRTP helps turn real-time communication into a more privacy-conscious service.
Protection Against Packet Tampering
SRTP can help protect against packet tampering by using authentication and integrity checks. If an attacker modifies a protected media packet, the receiver can detect the change and reject the packet.
This reduces the risk of manipulated media traffic being accepted by the endpoint. It also helps preserve trust in the communication session.
Packet integrity is essential when communication is used for decisions, instructions, or sensitive collaboration.
Reduced Risk of Replay Attacks
Replay attacks involve capturing valid packets and sending them again later. SRTP includes replay protection mechanisms that help detect and reject duplicated or old packets.
In real-time media, replayed packets could interfere with audio or video quality and create confusion. Replay protection makes this type of attack harder to perform successfully.
This benefit strengthens the overall trustworthiness of the media stream.
Better Security for Remote Communication
Remote communication is now common across cloud services, mobile users, work-from-home environments, branch offices, and internet-based collaboration platforms. SRTP helps protect media when communication crosses networks that the organization does not fully control.
This is useful for distributed teams, remote support, hosted PBX services, online meetings, remote education, and telehealth platforms.
As communication becomes more distributed, media-level encryption becomes more important.
Support for Compliance and Security Policies
Many organizations have policies requiring secure transmission of sensitive information. SRTP can help support these policies by protecting real-time voice and video traffic.
SRTP alone does not guarantee full compliance. Organizations must also consider signaling security, identity management, recording storage, access control, retention, endpoint security, and user policy.
However, SRTP is an important technical control for protecting media in communication systems.

Applications of SRTP
Enterprise Communication Systems
Enterprises use SRTP to secure internal and external voice communication. This may include desk phones, softphones, mobile clients, conference systems, and IP PBX media paths.
In enterprise environments, SRTP helps protect business discussions and reduce the risk of voice interception. It is especially useful when calls cross WAN links, cloud services, remote worker networks, or internet-based trunks.
For stronger protection, enterprises should combine SRTP with secure signaling, endpoint hardening, network segmentation, and access control.
Cloud PBX and Hosted Voice
Cloud PBX and hosted voice providers may use SRTP to secure media between customer endpoints, cloud platforms, and media servers. This is important because hosted voice traffic may cross public networks or shared service infrastructure.
SRTP helps service providers offer a more secure media transport option for customers. It can also help meet enterprise expectations for encrypted communication.
Customers should verify whether SRTP is supported end to end, which endpoints support it, and how key management is handled.
Healthcare and Telemedicine
Telemedicine platforms and healthcare communication systems may use SRTP to protect voice and video consultations. Healthcare communication can include sensitive personal and medical information, so media protection is important.
SRTP helps protect the live communication stream, while other controls protect patient identity, medical records, platform access, and stored recordings.
Secure media transport is one part of a broader healthcare privacy and security strategy.
Financial and Legal Communication
Financial institutions and legal organizations often discuss sensitive information through voice and video. This may include transactions, legal strategy, client details, compliance issues, account information, or confidential negotiations.
SRTP helps protect these communications while they are in transit. It can reduce the risk of media interception on untrusted or shared networks.
These organizations should also protect call recordings, user authentication, signaling, and endpoint devices.
Public Safety and Critical Operations
Public safety, utility, transportation, and industrial control environments may use SRTP to protect operational media. Voice and video streams in these environments may include incident details, response commands, field reports, and security-sensitive information.
SRTP provides media confidentiality and integrity, but operational systems must also prioritize reliability, availability, low latency, and emergency fallback. Secure media should not compromise mission-critical communication performance.
A balanced design considers both security and operational continuity.
SRTP Versus Related Protocols
SRTP Versus RTP
RTP carries real-time audio and video, but it does not provide strong security by itself. SRTP is a secure profile of RTP that adds protection for confidentiality, authentication, integrity, and replay resistance.
In simple terms, RTP moves the media, while SRTP secures the media. A system that uses RTP without SRTP may deliver the call successfully but still expose the content to interception.
For sensitive communication, SRTP is generally preferred over plain RTP.
SRTP Versus TLS
TLS and SRTP protect different parts of a communication system. TLS is commonly used to secure signaling, web traffic, APIs, and application sessions. SRTP is used to secure real-time media streams such as voice and video.
In SIP systems, TLS may protect SIP signaling, while SRTP protects the RTP media. Both may be needed because securing signaling alone does not automatically secure media content.
A secure communication design should identify which protocol protects which layer.
SRTP Versus VPN
A VPN can encrypt traffic between networks or devices, but it does not replace SRTP in every case. VPN encryption protects traffic within the VPN tunnel, while SRTP protects the media stream itself at the communication layer.
If media leaves the VPN boundary or passes through intermediate systems, SRTP may still provide important protection. SRTP is also useful when endpoints communicate through cloud services or external networks.
VPN and SRTP can be complementary. A VPN protects the network path, while SRTP protects the real-time media session.
SRTP Versus ZRTP and DTLS-SRTP
SRTP protects the media stream, while ZRTP and DTLS-SRTP are related to key agreement methods for securing media. DTLS-SRTP is commonly used in WebRTC and other systems to establish SRTP keying material.
This distinction matters because media encryption and key negotiation are connected but not identical. A system needs both a secure media protection method and a secure method for establishing the keys used by that method.
When evaluating a product or platform, users should ask how SRTP is enabled and how SRTP keys are exchanged.
Deployment Considerations
Endpoint Compatibility
SRTP must be supported by the endpoints and systems involved in the call. IP phones, softphones, conferencing clients, media servers, SBCs, gateways, and PBX platforms must be configured with compatible SRTP settings.
If one endpoint requires SRTP and another does not support it, the call may fail or fall back to plain RTP depending on policy. Administrators should decide whether SRTP is mandatory, optional, or negotiated case by case.
Compatibility testing is important before enabling SRTP across a large environment.
Key Management and Signaling Security
SRTP depends on secure key management. If keys are exchanged through signaling, the signaling path should be protected. If DTLS-SRTP is used, the media path key negotiation should be validated. Weak key handling can undermine otherwise strong media protection.
Administrators should understand how their system negotiates SRTP keys, how certificates or keys are trusted, and how failed negotiation is handled. This is especially important in mixed-vendor deployments.
Secure signaling and secure key management are essential parts of SRTP deployment.
Firewall and NAT Traversal
SRTP media streams still need to traverse firewalls, NAT devices, SBCs, and media relays. Encryption protects the media payload, but it can also affect how network tools inspect or manipulate traffic.
Session Border Controllers and media relay systems are often used to manage secure media traversal between internal networks, service providers, and remote users. Administrators should ensure that these devices support SRTP correctly.
Firewall rules, port ranges, NAT traversal methods, and media relay policies should be tested carefully.
Performance and Quality
SRTP adds security processing to real-time media, but it is designed to be efficient. Still, devices and servers must have enough processing capacity for encryption, authentication, and decryption, especially during high call volume or conferencing.
Performance planning should include endpoint CPU capacity, media server load, transcoding requirements, packet loss, jitter, latency, and concurrent sessions. Poor network quality can still affect SRTP calls even when encryption works correctly.
Secure media must also remain clear, stable, and low-latency for users.
A successful SRTP deployment requires compatible endpoints, secure key management, protected signaling, firewall planning, and real-world call quality testing.
Common Challenges in SRTP Deployment
Mixed Endpoint Support
Some communication environments include old phones, new softphones, gateways, mobile clients, conferencing systems, and third-party trunks. Not all devices may support the same SRTP options or keying methods.
Mixed support can create negotiation failures or inconsistent security. Administrators should identify which endpoints support SRTP, which require firmware updates, and which may need replacement or gateway handling.
A clear migration plan helps avoid unexpected call failures.
Misconfigured Key Exchange
Key exchange problems are a common source of SRTP failure. Calls may connect but have no audio, one-way audio, or failed media negotiation if SRTP parameters do not match between systems.
Troubleshooting should check signaling messages, endpoint settings, certificates, crypto suites, SBC behavior, and whether the system expects mandatory or optional SRTP.
Secure media configuration should be tested with representative call paths before production rollout.
False Sense of Security
Enabling SRTP does not automatically secure the entire communication system. Signaling may still be exposed, endpoints may be compromised, recordings may be stored insecurely, or users may connect through weak authentication.
SRTP protects media in transit. It should be part of a layered security design that includes signaling protection, strong identity, endpoint security, access control, logging, secure recording, and network monitoring.
Understanding the boundary of SRTP protection prevents unrealistic assumptions.
Troubleshooting Encrypted Media
Encryption can make troubleshooting more difficult because administrators cannot inspect media content directly. Tools may still show packet flow, timing, ports, packet loss, and negotiation details, but media payload inspection is intentionally limited.
Troubleshooting SRTP often requires checking metadata, signaling negotiation, endpoint logs, SBC logs, packet counters, certificates, and test calls. Administrators should have procedures for diagnosing secure media without weakening security.
Secure systems require secure troubleshooting methods.
Best Practices for SRTP
Use SRTP with Secure Signaling
SRTP should be combined with secure signaling wherever possible. In SIP systems, this often means protecting SIP signaling with TLS. If signaling carries keying information, signaling protection becomes especially important.
Secure media and secure signaling work together. Media encryption protects call content, while signaling protection helps protect call setup, identity, routing, and negotiation details.
A complete secure communication design should address both.
Prefer Strong Key Management
Key management should be selected carefully. DTLS-SRTP is widely used in WebRTC-style environments, while other environments may use different methods depending on platform support.
Administrators should avoid weak or outdated keying methods and should verify that keys are not exposed unnecessarily. Certificates, trust models, and endpoint validation should be documented.
Strong key management is one of the most important parts of SRTP security.
Make Security Policy Clear
Organizations should decide whether SRTP is required, preferred, or optional. If SRTP is optional, some calls may fall back to plain RTP. If SRTP is mandatory, calls with unsupported endpoints may fail.
The right policy depends on risk, device compatibility, user needs, compliance requirements, and operational tolerance for failed calls. High-security environments may require SRTP for all supported media paths.
Clear policy prevents inconsistent deployment.
Test End-to-End Media Paths
SRTP should be tested across real call paths. Internal extension-to-extension calls, remote worker calls, trunk calls, conference calls, contact center calls, WebRTC sessions, mobile clients, and gateway calls may behave differently.
Testing should verify call setup, two-way audio, video quality, recording behavior, conferencing, transfer, hold, NAT traversal, and fallback behavior. Security should not be tested only in a lab environment.
End-to-end testing helps confirm that SRTP works in real operational conditions.
Monitor and Maintain Secure Media
Secure media should be monitored as part of normal communication operations. Administrators should review call quality reports, failed negotiation logs, endpoint compatibility, certificate expiration, SBC logs, and policy exceptions.
Systems change over time. New endpoints, firmware updates, service provider changes, firewall changes, or cloud migration may affect SRTP behavior.
Regular review helps keep SRTP reliable and secure after initial deployment.
Conclusion
Secure Real-Time Transport Protocol, or SRTP, is a security profile for protecting real-time media streams such as voice and video. It adds encryption, message authentication, integrity protection, and replay protection to RTP-based communication.
SRTP works by protecting RTP media packets while preserving the low-latency behavior needed for real-time calls and conferencing. It can also protect related control traffic through SRTCP. However, SRTP requires proper key management through methods such as DTLS-SRTP or other supported keying approaches.
SRTP is used in secure VoIP, WebRTC, video conferencing, contact centers, telemedicine, enterprise communications, emergency dispatch, and hosted communication platforms. Its main benefits include improved privacy, protection against tampering, replay resistance, secure remote communication, and support for security policies. For best results, SRTP should be deployed with secure signaling, compatible endpoints, strong key management, tested firewall traversal, and ongoing monitoring.
FAQ
What is SRTP in simple terms?
SRTP is a secure version of RTP that protects real-time voice and video streams. It encrypts media packets and can also provide authentication, integrity checking, and replay protection.
It is commonly used in VoIP, WebRTC, video conferencing, and secure communication systems.
What is the difference between RTP and SRTP?
RTP carries real-time audio and video, but it does not provide strong security by itself. SRTP is a secure profile of RTP that adds encryption and other security protections to the media stream.
In simple terms, RTP transports media, while SRTP secures that media.
Does SRTP secure SIP signaling?
No. SRTP secures the media stream, not the SIP signaling messages. SIP signaling should be protected separately, commonly with TLS in SIP-based systems.
A secure communication design should protect both signaling and media.
Where is SRTP commonly used?
SRTP is commonly used in VoIP systems, IP PBX platforms, SIP phones, WebRTC applications, video conferencing, cloud PBX services, contact centers, telemedicine, and emergency communication systems.
It is especially useful when voice or video traffic crosses untrusted or shared networks.
Is SRTP enough to make communication fully secure?
SRTP protects media in transit, but it is not the whole security solution. Systems also need secure signaling, strong authentication, endpoint protection, secure recordings, access control, key management, and monitoring.
SRTP is an important layer in a broader communication security architecture.