Most digital systems do not work alone. They exchange data, request services, trigger actions, and connect with other platforms through APIs.
An Application Programming Interface, commonly called an API, is a set of rules, definitions, protocols, and tools that allows different software systems to communicate with each other. It defines how one application can request data or services from another application, and how the receiving system should respond.
APIs are widely used in websites, mobile apps, cloud platforms, payment systems, enterprise software, IoT platforms, communication systems, e-commerce platforms, logistics systems, data dashboards, and smart devices. Without APIs, many modern digital services would become isolated systems that cannot exchange information efficiently.
The Basic Meaning of an API
An API acts as an interface between software components. It allows one system to access specific functions or data from another system without exposing all internal code, database structure, or backend logic. This separation makes integration safer, cleaner, and easier to manage.
For example, a weather app may use an API to request weather data from a weather service. A payment page may use an API to connect with a payment gateway. A logistics platform may use APIs to check shipping status, update order records, and notify customers automatically.
Interface Between Software Systems
The word “interface” is important. An API does not usually give direct access to the full internal system. Instead, it provides controlled access through defined request and response methods. This allows developers to build new features while keeping the core system protected.
In practice, APIs help systems communicate in a standardized way. One application sends a request, the API receives it, the server processes it, and then a response is returned. The response may contain data, confirmation, an error message, or a command result.
Why APIs Are Used
APIs are used because modern software needs connection. A single application may need user login, maps, payment processing, messaging, cloud storage, AI services, analytics, video, device data, or business system integration. Building every function from scratch would be slow, expensive, and difficult to maintain.
With APIs, developers can reuse existing services, connect different platforms, automate workflows, and create more powerful applications. This is one of the main reasons APIs have become a core foundation of digital transformation.
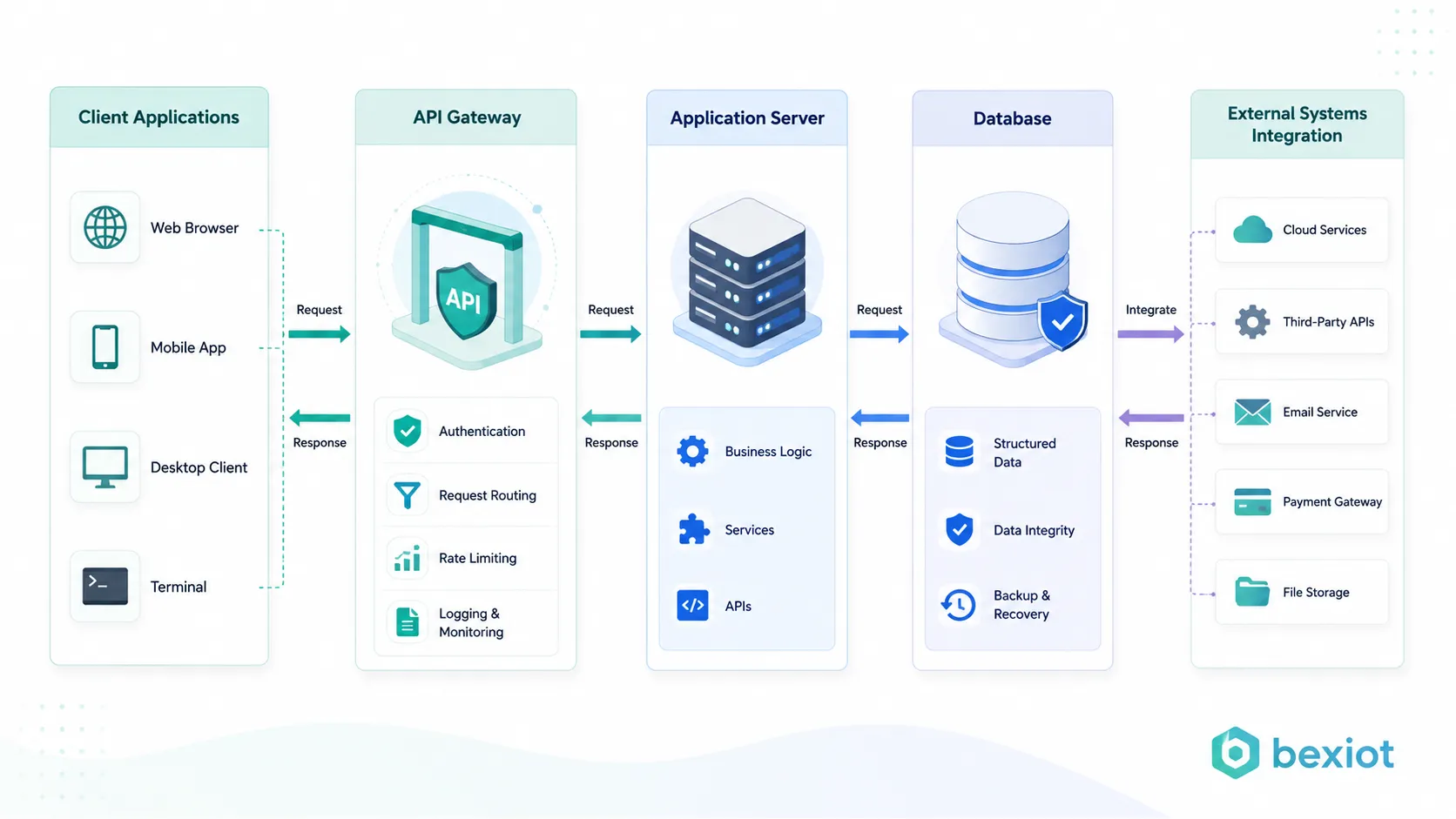
How API Communication Works
API communication usually follows a request-and-response model. A client application sends a request to an API endpoint. The server receives the request, checks whether it is valid, processes the required logic, and sends back a response in a structured format.
This process may happen in milliseconds, but it can involve many backend steps. The server may verify user identity, check permissions, query a database, call another service, process data, write logs, and return the final result.
API Endpoint and Request
An API endpoint is a specific address where a client can access a function or resource. For example, one endpoint may return user information, another may submit an order, and another may update device status. Each endpoint has a defined purpose.
The request usually includes a method, endpoint address, headers, parameters, and sometimes a request body. In web APIs, common methods include GET for retrieving data, POST for creating data, PUT or PATCH for updating data, and DELETE for removing data.
Processing and Response
After the server receives the request, it processes the logic behind the API. This may include data validation, authentication, business rule execution, database operation, or communication with another service. The server then returns a response to the client.
The response may use formats such as JSON or XML. JSON is widely used because it is lightweight, readable, and easy for web and mobile applications to process. A response normally includes requested data, status information, or an error code when the request fails.
Authentication and Permission Control
Many APIs require authentication before access is allowed. Common methods include API keys, OAuth tokens, JWT tokens, session credentials, and signature-based verification. These methods help confirm who is making the request.
Permission control is equally important. A user may be allowed to view data but not delete it. A partner system may be allowed to access order status but not financial records. APIs must define access rules clearly to protect business data and system security.
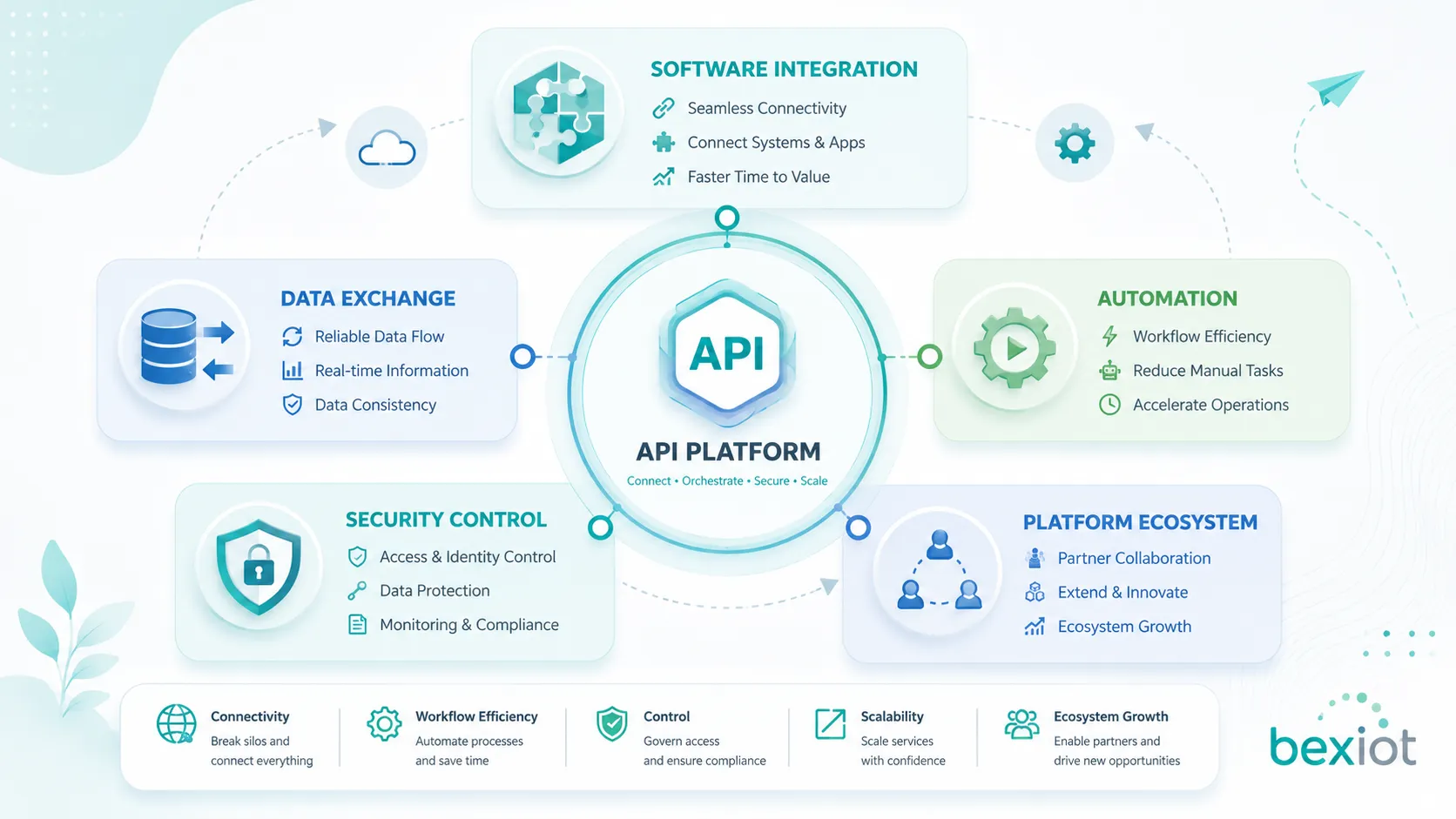
Main Functions of an API
APIs provide many functions beyond simple data exchange. They help applications share services, automate processes, connect third-party platforms, control access, and extend system capabilities without rebuilding the entire software architecture.
Data Exchange
One of the most common API functions is data exchange. APIs allow one system to retrieve, submit, update, or synchronize data with another system. This is used in customer management, order processing, inventory control, financial reporting, device monitoring, and many other scenarios.
For example, an online store may use APIs to synchronize product stock with a warehouse system. A mobile app may use APIs to display user account data. A dashboard may use APIs to collect data from multiple business platforms and display it in one interface.
Service Access
APIs allow applications to access services provided by other systems. These services may include payment processing, map positioning, identity verification, messaging, cloud storage, translation, AI analysis, email delivery, video streaming, or file conversion.
This service-based model allows developers to focus on their core application while relying on specialized platforms for supporting functions. It also helps companies launch new services faster and reduce development costs.
Workflow Automation
APIs are widely used for automation. When one system changes, another system can be updated automatically. For example, when a customer places an order, APIs can trigger inventory deduction, payment confirmation, delivery scheduling, invoice creation, and customer notification.
Automation reduces manual work, improves accuracy, and speeds up business operations. In enterprise environments, API-based automation is often used to connect CRM, ERP, HR, finance, logistics, support, and reporting systems.
System Integration
APIs make it possible to connect systems from different vendors, departments, or technology stacks. A company may use separate software for sales, finance, operations, communication, security, and customer service. APIs help these platforms exchange information.
This integration value is especially important for large organizations. Instead of replacing every system, companies can use APIs to connect existing platforms and build a more unified digital workflow.
Common Types of APIs
APIs can be classified in different ways according to access scope, technology style, and system purpose. Understanding these types helps developers, project managers, and system integrators choose the right approach for each application.
| API Type | Main Purpose | Common Use |
|---|---|---|
| Public API | Open access for external developers or partners | Payment services, maps, social platforms, cloud services |
| Private API | Internal use within one company or system | Enterprise integration, internal dashboards, backend services |
| Partner API | Controlled access for selected business partners | Supply chain, logistics, finance, channel platforms |
| Composite API | Combines multiple service calls into one workflow | Order processing, mobile app backend, service orchestration |
REST API
REST API is one of the most common API styles. It usually uses HTTP methods and resource-based URLs to perform operations. REST APIs are widely used in web applications, mobile apps, cloud services, IoT platforms, and enterprise systems.
REST is popular because it is relatively simple, scalable, and easy to understand. It commonly returns data in JSON format, making it convenient for front-end applications and backend services to process.
SOAP API
SOAP API is an older but still important API style that uses XML-based messaging and strict standards. It is often found in enterprise, banking, telecom, government, and legacy system environments where formal structure and reliability are important.
SOAP can support strong contract definitions and enterprise-level messaging requirements. However, it is usually more complex and less lightweight than REST for many modern web and mobile applications.
GraphQL API
GraphQL allows clients to request exactly the data they need. Instead of using multiple fixed endpoints, a client sends a query that describes the desired data structure. This can reduce over-fetching and under-fetching of data.
GraphQL is useful for applications with complex data relationships, such as dashboards, social platforms, content systems, and mobile applications. It gives front-end teams more flexibility, but it also requires careful performance and security design.
WebSocket API
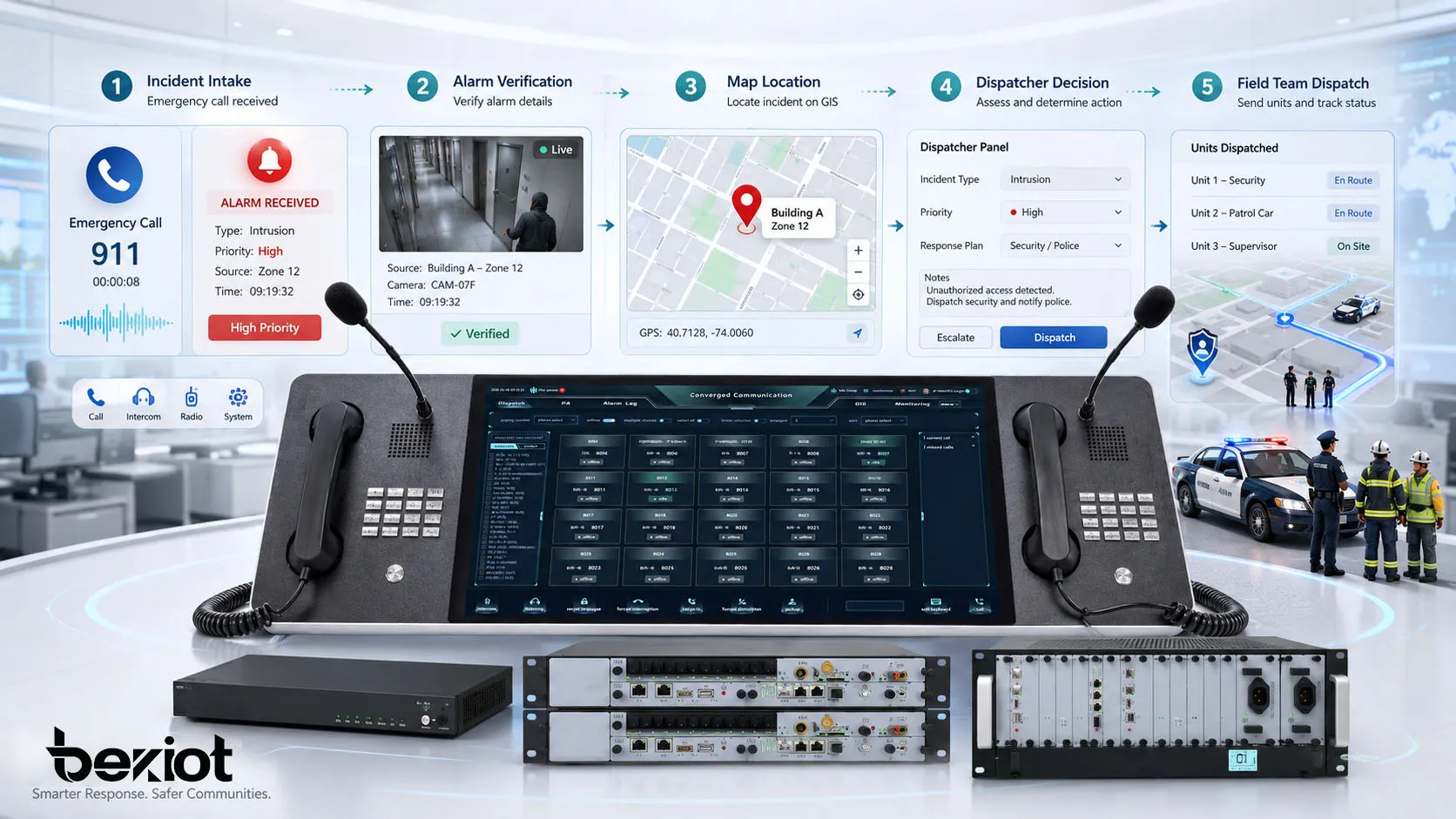
WebSocket APIs support real-time two-way communication between client and server. Unlike traditional request-and-response APIs, WebSocket connections can stay open, allowing both sides to send data continuously.
This is useful for chat systems, live monitoring, online games, financial trading dashboards, control platforms, real-time alerts, and collaborative applications where immediate updates are required.
System Value for Digital Architecture
The value of APIs is not limited to developers. APIs shape how digital systems are built, expanded, secured, and connected. A well-designed API strategy can improve business flexibility and reduce technology barriers between systems.
Reducing System Isolation
Without APIs, software systems often become isolated data islands. Teams may need manual exports, repeated data entry, custom scripts, or direct database access to exchange information. These methods are inefficient and risky.
APIs provide a structured way to connect systems. They allow data to move between platforms more securely and consistently, helping organizations build unified workflows across departments and applications.
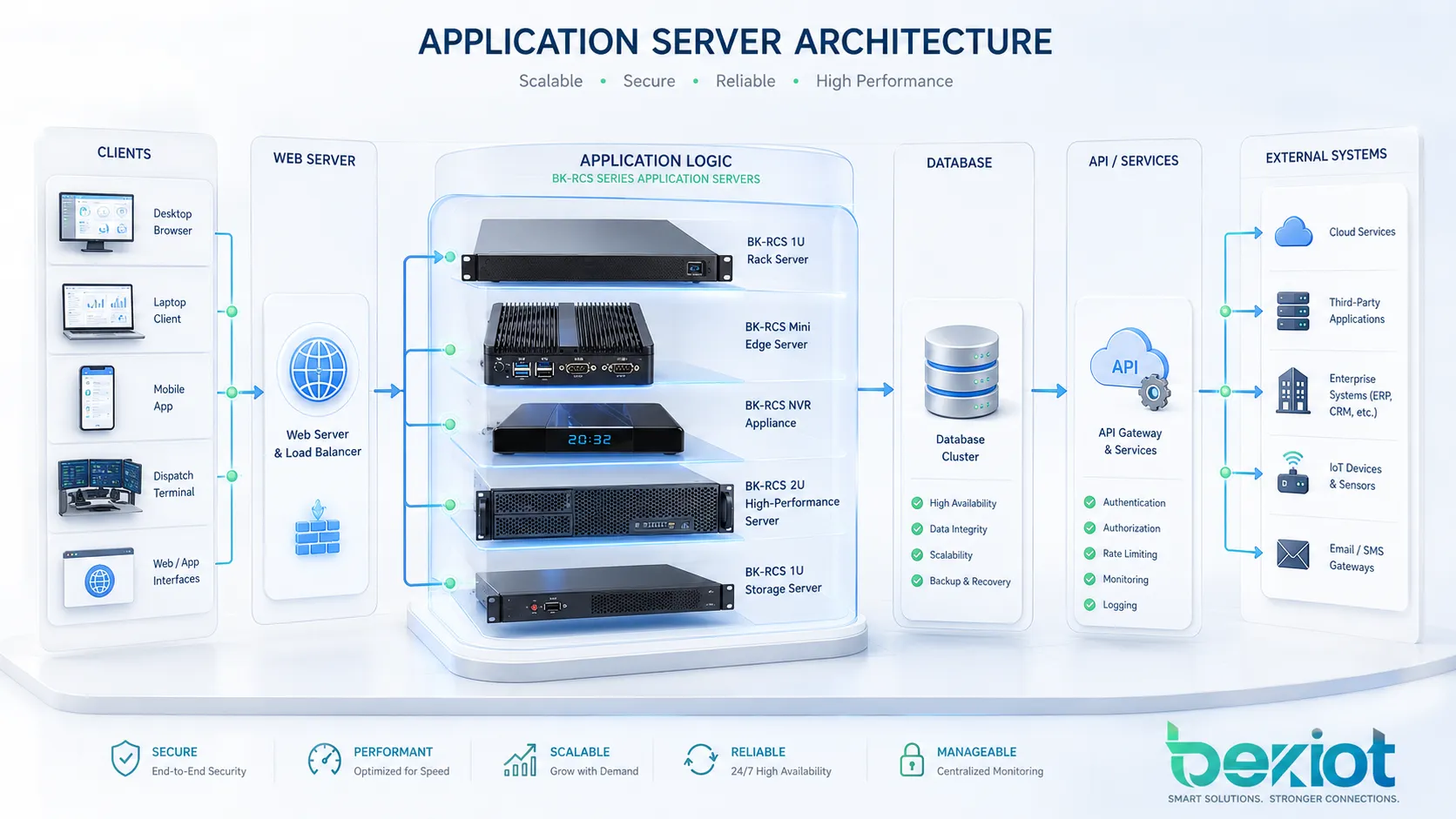
Supporting Scalable Development
APIs allow development teams to separate front-end interfaces, backend services, databases, and third-party integrations. This separation makes systems easier to expand. A web app, mobile app, and partner platform can all use the same API layer.
This is especially useful when companies need to add new channels. Instead of rebuilding business logic for every interface, developers can expose reusable API services and connect them to different applications.
Improving Security Management
APIs help control how data and services are accessed. Instead of allowing direct database connections or unrestricted system access, organizations can expose only the functions that are needed. Authentication, permission control, rate limiting, logging, and encryption can be applied at the API layer.
This controlled access model improves security and makes auditing easier. It also helps organizations manage external partners, internal teams, and third-party applications with clearer boundaries.
Enabling Platform Ecosystems
Many successful digital platforms grow because they provide APIs for developers and partners. These APIs allow other companies to build integrations, extensions, applications, and services around the core platform.
This ecosystem model is common in cloud computing, e-commerce, logistics, communication, payment, social media, and enterprise software. APIs turn a single product into a platform that can support broader business cooperation.
Applications in Real-World Systems
APIs are used almost everywhere in modern software. They connect visible user interfaces with invisible backend services. They also connect business systems with devices, partners, customers, and cloud platforms.
Websites and Mobile Apps
Most websites and mobile apps use APIs to display data, submit forms, process payments, manage user accounts, upload files, send messages, and retrieve content. The user sees a smooth interface, while the API handles communication with backend systems.
For example, a food delivery app may use APIs for restaurant listings, user login, map location, order placement, payment, driver tracking, and customer notifications. Each feature may depend on one or more APIs.
Enterprise Software Integration
Enterprise systems use APIs to connect CRM, ERP, finance, inventory, HR, customer support, business intelligence, and document management platforms. This reduces duplicate data entry and improves process visibility.
For example, when a sales order is created in a CRM system, an API can send the order to an ERP system, update inventory, generate an invoice, and notify the logistics team. This creates a smoother workflow across departments.
IoT and Device Management
IoT platforms use APIs to collect data from devices, send control commands, update device status, and connect sensor data with dashboards or alert systems. APIs are important for smart buildings, industrial monitoring, energy management, fleet tracking, and environmental monitoring.
In these scenarios, APIs help bridge the physical and digital worlds. Sensors and devices generate data, while software platforms analyze, display, and act on that data through API-based communication.
Cloud Services and Microservices
Cloud platforms rely heavily on APIs. Developers use APIs to create servers, store files, manage databases, send notifications, control security settings, and monitor application performance. Many cloud operations are API-driven.
Microservice architecture also depends on APIs. Instead of one large application doing everything, smaller services communicate with each other through APIs. This improves flexibility, but it also requires strong API management, monitoring, and security practices.
Payment, Logistics, and Customer Services
Payment gateways use APIs to process transactions, verify cards, create refunds, check payment status, and support fraud control. Logistics companies use APIs to calculate shipping rates, create labels, track packages, and update delivery status.
Customer service platforms use APIs to connect tickets, chat tools, CRM records, user accounts, and notification systems. This helps support teams see customer information and respond more efficiently.
API Management and Governance
As the number of APIs grows, organizations need API management. API management includes design standards, documentation, access control, versioning, monitoring, rate limiting, security policies, and lifecycle maintenance.
Without governance, APIs can become inconsistent, insecure, poorly documented, or difficult to maintain. A good API strategy makes integration easier for developers and safer for the organization.
Documentation and Developer Experience
Good API documentation explains what each endpoint does, what parameters are required, what response format is returned, what error codes mean, and how authentication works. Clear documentation reduces integration time and prevents repeated support questions.
Developer experience matters because APIs are products for developers. If an API is hard to understand, unstable, or poorly documented, developers may avoid using it or implement it incorrectly.
Version Control
APIs change over time. New fields may be added, old functions may be removed, and security rules may change. Version control helps protect existing integrations while allowing the API to improve.
For example, an organization may maintain version 1 for older clients while releasing version 2 with new features. This prevents sudden service disruption and gives partners time to update their systems.
Monitoring and Rate Limiting
API monitoring tracks usage, errors, response time, traffic spikes, failed requests, and abnormal activity. This helps teams detect performance problems and security risks quickly.
Rate limiting controls how many requests a client can send during a certain period. It helps protect the server from overload, accidental abuse, or malicious traffic. For public APIs, rate limiting is especially important.
Security Considerations
APIs can expose valuable data and critical functions, so security must be designed carefully. A weak API may allow unauthorized access, data leakage, service abuse, or system compromise.
Authentication and Authorization
Authentication confirms the identity of the user or system making the request. Authorization determines what that user or system is allowed to do. Both are required for secure API access.
For example, an authenticated user may be allowed to view their own orders but not view all customer records. A partner API client may be allowed to create shipping labels but not change product pricing. These rules should be enforced consistently.
Data Protection
APIs should protect data during transmission and processing. HTTPS encryption is commonly used to secure communication between client and server. Sensitive data should be minimized, masked, encrypted, or protected according to business and regulatory requirements.
API responses should not expose unnecessary internal details. Error messages should be useful for troubleshooting but should not reveal database structure, system paths, tokens, passwords, or internal server information.
Input Validation
APIs should validate all incoming data. Invalid, unexpected, or malicious input can cause security vulnerabilities, data corruption, or application errors. Input validation helps ensure that the server only processes safe and expected data.
Common protections include checking data type, length, format, allowed values, file type, request size, and permission scope. Validation should happen on the server side even if the client also performs checks.
Common Challenges and Mistakes
API projects can fail when the design is unclear, documentation is incomplete, security is weak, or system performance is ignored. APIs should be treated as long-term service interfaces, not temporary connection points.
Poorly Designed Endpoints
A confusing endpoint structure makes APIs hard to use and maintain. If endpoint names are inconsistent, request methods are unclear, or response formats vary without reason, developers may make integration errors.
Good API design should be predictable. Similar functions should follow similar patterns, and response structures should be consistent. This improves maintainability and reduces development mistakes.
Ignoring Backward Compatibility
Changing an API without warning can break existing applications. If a field is removed, a response format changes, or an authentication rule is modified suddenly, clients depending on the API may fail.
Organizations should use versioning, release notes, deprecation notices, and migration guides when changing important APIs. This is especially important for partner and public APIs.
Weak Error Handling
APIs should return clear and useful error messages. A generic failure response may not help developers understand what went wrong. At the same time, error messages should not reveal sensitive internal information.
Good error handling includes proper status codes, readable messages, request identifiers, and troubleshooting guidance. This helps developers fix problems faster and helps support teams analyze issues more effectively.
Best Practices for API Design
Good API design focuses on clarity, security, consistency, performance, and long-term maintainability. Whether the API is public, private, or partner-facing, it should be easy to understand and safe to operate.
| Best Practice | Purpose | Practical Result |
|---|---|---|
| Use clear naming | Make endpoints easy to understand | Reduces developer confusion |
| Protect access | Control who can use the API | Improves data and system security |
| Document every endpoint | Help developers integrate correctly | Shortens development and support time |
| Use versioning | Support updates without breaking clients | Improves long-term maintainability |
| Monitor usage | Track performance and abnormal activity | Improves reliability and troubleshooting |
Design for Real Use Cases
An API should be designed around real business and technical use cases. It should provide the data and functions that developers actually need, without exposing unnecessary complexity.
Before building an API, teams should define who will use it, what actions they need to perform, what data they need, how often requests will be made, and what security level is required. This planning improves the final design.
Keep Responses Consistent
Consistent response formats make APIs easier to use. Developers should not have to handle completely different structures for similar operations. Standardized success responses, error responses, pagination, filtering, and status codes improve integration quality.
Consistency also helps automated testing, monitoring, documentation, and SDK development. A predictable API is easier to maintain as the system grows.
Plan for Growth
API usage can grow quickly when more applications, partners, devices, or users depend on the service. The architecture should support scaling, caching, load balancing, rate limiting, and performance monitoring.
Planning for growth also means designing APIs that can evolve. Fields, endpoints, and business logic may change over time, so versioning and backward compatibility should be considered from the beginning.
FAQ
What is an Application Programming Interface API?
An Application Programming Interface, or API, is a defined way for software systems to communicate. It allows one application to request data, services, or actions from another system through controlled rules and formats.
What is the main function of an API?
The main function of an API is to enable communication and integration between software systems. APIs can exchange data, trigger workflows, provide access to services, support automation, and connect platforms securely.
What is an API endpoint?
An API endpoint is a specific address or access point where a client application can request a certain function or resource. Each endpoint usually has a defined purpose, such as retrieving user data, submitting an order, or updating device status.
What is the difference between REST API and SOAP API?
REST API is usually simpler and commonly uses HTTP methods with JSON data, making it popular for web, mobile, and cloud services. SOAP API uses XML-based messaging and stricter standards, often appearing in enterprise and legacy environments.
Why are APIs important for businesses?
APIs help businesses connect systems, automate workflows, reduce manual work, improve data sharing, support partner integration, and build scalable digital platforms. They make software ecosystems more flexible and easier to expand.
Are APIs secure?
APIs can be secure when they use proper authentication, authorization, encryption, input validation, logging, rate limiting, and monitoring. Poorly designed or unprotected APIs can create serious security risks, so API security should be planned carefully.