HTTPS secure access refers to the use of HTTPS—Hypertext Transfer Protocol Secure—to protect data exchanged between a client and a server. In practical terms, it means a browser, mobile app, or web-enabled device connects to a website, portal, API, or management interface over HTTP running on top of TLS (Transport Layer Security) instead of plain HTTP. This creates a protected communication channel that helps prevent eavesdropping, tampering, and some impersonation risks during transmission.
Although the phrase HTTPS secure access is commonly used in product pages and IT documentation, it does not describe a separate network protocol beyond HTTPS itself. It usually refers to a secure web-based access method used for user logins, cloud dashboards, enterprise portals, device web management, and API calls. In other words, the core technology is HTTPS, while secure access describes the way it is applied in real environments.
HTTPS remains fundamental because web access is now the default entry point for many business systems. Employees sign in to SaaS platforms through browsers, administrators manage gateways and IP PBX systems through web consoles, customers use e-commerce sites and self-service portals, and machines communicate with cloud platforms through web APIs. In all of these situations, transport security is not an optional enhancement. It is a baseline requirement for privacy, trust, and operational security.
What Is HTTPS Secure Access?
At a technical level, HTTPS is the encrypted form of HTTP. The application still uses HTTP methods and resources, but the session runs through TLS so that requests and responses are protected while traveling across untrusted networks such as the public internet, shared Wi-Fi, or third-party carrier infrastructure.
For users, HTTPS secure access is often identified by a padlock icon, an https:// URL, and a valid digital certificate presented by the server. For administrators, it means the web service has been configured with TLS, a valid certificate chain, modern cipher suites, and supporting security controls such as HSTS, secure cookies, and certificate lifecycle management.

HTTPS secure access uses HTTP over TLS so browsers and applications can communicate with web servers through an encrypted and authenticated session.
How HTTPS Secure Access Works
When a client visits an HTTPS-enabled address, it starts a TLS negotiation before normal HTTP data is exchanged. During this process, the server presents a digital certificate that helps the client verify the server identity for the requested domain. The client and server then agree on cryptographic parameters and establish shared session keys. Once the secure session is in place, ordinary HTTP requests and responses continue inside that encrypted tunnel.
In practical deployments, the process usually involves several linked elements: DNS resolution, TCP or QUIC connectivity, TLS negotiation, certificate validation, and then the protected application exchange. If any of these steps is misconfigured—for example, the certificate is expired, the hostname does not match, or an outdated TLS configuration is still enabled—users may see browser warnings or the connection may fail altogether.
The most important result of this process is not just encryption. HTTPS is valuable because it combines three security goals that matter in day-to-day operations:
Confidentiality: Data sent between the client and server is encrypted in transit.
Integrity: Attackers should not be able to silently alter traffic without detection.
Authentication: The client can verify that it is talking to the intended site or service, subject to certificate trust and proper validation.
Key Features of HTTPS Secure Access
1. Encrypted Data Transmission
The most visible feature of HTTPS secure access is encryption during transport. Login credentials, session cookies, account data, configuration commands, API tokens, and business transactions are far less exposed than they would be over plain HTTP. This is especially important for remote work, mobile access, and public or semi-trusted network environments.
Encryption does not make an application automatically secure, but it does remove one of the most serious weaknesses of plain web access: readable traffic in transit. For many systems, that alone changes the threat profile substantially.
2. Server Authentication Through Certificates
HTTPS depends on digital certificates to help clients validate server identity. A correctly issued and properly installed certificate is what allows a browser or application to trust that the service reached at a certain domain is the intended one. This is one reason certificate management matters so much in production systems.
Without sound certificate handling, organizations can still face outages or trust failures even when HTTPS is technically enabled. Expired certificates, incomplete certificate chains, hostname mismatches, and weak operational processes are among the most common real-world issues.
3. Message Integrity Protection
HTTPS helps ensure that content is not modified in transit without detection. That matters not only for passwords and personal data, but also for downloaded files, scripts, configuration pages, and API responses. In other words, HTTPS is not just about secrecy; it also helps preserve the reliability of what the user receives.
4. Support for Secure Web Sessions
Modern websites and enterprise systems rely heavily on authenticated sessions. HTTPS helps protect cookies, tokens, and session identifiers from simple interception attacks. It also works with browser-side protections such as the Secure cookie attribute and server policies such as HSTS, which tells browsers to prefer HTTPS-only access for future visits.
In real deployments, HTTPS secures login pages, admin sessions, APIs, and browser-based access to cloud or on-premises systems.
5. Better Browser Trust and Platform Compatibility
Today, HTTPS is no longer a premium feature for banking or e-commerce alone. Browsers, search engines, SaaS platforms, and modern web APIs increasingly assume secure transport by default. Many advanced browser capabilities are available only in secure contexts, and unsecured HTTP pages are often flagged as risky or limited in functionality.
This shift means HTTPS secure access is now part of basic digital infrastructure. If a platform still relies on plain HTTP for logins, device management, or customer interaction, it often appears outdated and potentially unsafe even before a formal security review begins.
6. Compatibility With Security Policies and Compliance Needs
Organizations often need HTTPS not only for user confidence, but also for policy alignment. Internal security baselines, customer procurement requirements, cyber insurance expectations, and sector-specific rules frequently assume encrypted web access. HTTPS therefore supports both technical protection and governance requirements.
Common Components Behind HTTPS Secure Access
Although the user experience may look simple, reliable HTTPS access usually depends on a broader support stack:
TLS certificates issued and renewed through a controlled process
Web servers, reverse proxies, or load balancers configured for modern TLS
DNS and domain ownership aligned with certificate names
Application settings for secure cookies, redirects, and trusted origins
Monitoring for certificate expiry, weak configurations, and handshake failures
Optional controls such as HSTS, mutual TLS, WAF, and access policies
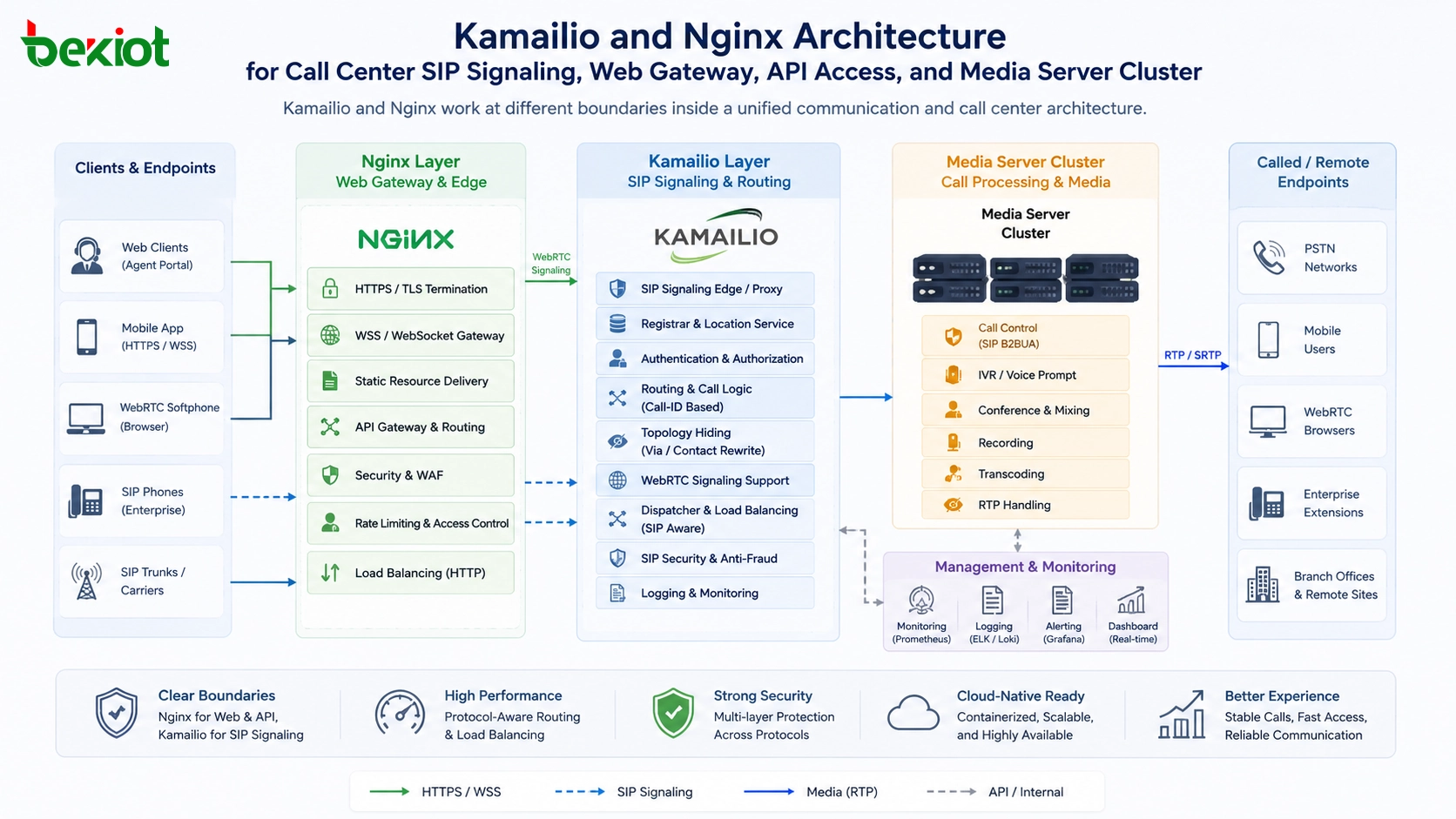
In enterprise environments, HTTPS secure access is often terminated at a reverse proxy, application delivery controller, or ingress gateway instead of the application server itself. That architecture can simplify certificate management and centralize transport security, though it must be designed carefully so that the trusted boundary remains clear.
Applications of HTTPS Secure Access
Website and Portal Access
Public websites, company portals, knowledge bases, customer self-service pages, and content platforms all rely on HTTPS to protect browsing sessions and form submissions. Even when the content itself is not highly sensitive, authenticated sessions, search terms, and user behavior still benefit from protected transport.
SaaS and Cloud Platform Login
Most business software is now delivered through browser-based interfaces. CRM, ERP, HR systems, ticketing platforms, file-sharing tools, and analytics dashboards all depend on HTTPS secure access to protect authentication flows and day-to-day user activity.
API Security
APIs are among the most important applications of HTTPS. Mobile apps, IoT platforms, web front ends, and third-party integrations commonly send tokens, business data, and control instructions through HTTPS APIs. In these cases, transport security is foundational even when additional authentication and authorization layers are also in place.
Remote Device Management
Many network devices, industrial gateways, routers, IP PBX systems, cameras, and communication terminals provide browser-based administrative interfaces. HTTPS secure access helps protect configuration sessions, account credentials, firmware operations, and management traffic when engineers administer devices locally or remotely.

HTTPS secure access is widely used for cloud dashboards, browser-based administration, and secure web control of connected devices and communication systems.
Online Transactions and Service Delivery
Banking, online payments, reservations, telemedicine, digital government services, and customer onboarding all depend on secure web sessions. In these scenarios, HTTPS protects the transmission layer while the application itself handles business logic, access control, and data processing.
Enterprise Intranet and Extranet Systems
Internal dashboards, partner portals, supplier systems, and branch-office web applications also use HTTPS because private network boundaries alone are no longer enough. Hybrid work and cloud integration have made secure application-layer access more important than legacy trust assumptions based only on location.
Advantages of HTTPS Secure Access in Real Environments
Organizations adopt HTTPS not only because it is technically correct, but because it solves practical problems. It reduces the risk of exposed credentials on untrusted links, improves user confidence, supports modern browser behavior, and helps standardize remote access to web-based systems. For distributed organizations, it also creates a cleaner path to secure access without forcing every user into a full VPN workflow for every web session.
That said, HTTPS should not be mistaken for complete application security. It protects data in transit, not every layer of the system. A web application can still have weak passwords, broken access controls, vulnerable APIs, insecure code, or poor server hygiene even if the connection is protected by TLS. The right way to view HTTPS secure access is as a baseline control—essential, but not sufficient by itself.
Deployment Considerations and Best Practices
Use valid, trusted certificates: Avoid expired, self-signed, or mismatched certificates in production user-facing services unless the environment is tightly controlled.
Redirect HTTP to HTTPS: Users and links should consistently land on the encrypted version of the service.
Enable HSTS where appropriate: This helps browsers remember that a host should be accessed only over HTTPS.
Prefer modern TLS configurations: Remove obsolete protocol versions and weak cryptographic settings.
Protect cookies and sessions: Use secure cookie attributes and strong session handling practices.
Monitor certificate lifecycle: Expiry and renewal failures are common operational causes of service disruption.
Remember the rest of the stack: HTTPS complements authentication, authorization, application hardening, logging, and security testing rather than replacing them.
HTTPS Secure Access vs. Plain HTTP
The difference between HTTPS and plain HTTP is not merely cosmetic. HTTP sends application data without transport-layer encryption, which makes it much easier for intermediaries to observe or alter traffic under the wrong conditions. HTTPS adds TLS to protect that communication path and provide a more trustworthy connection model.
For that reason, plain HTTP is increasingly unsuitable for login pages, account sessions, device administration, customer services, and API exchange. In modern environments, using HTTP for anything sensitive is generally treated as a security weakness rather than a neutral design choice.
FAQ
Is HTTPS the same as SSL?
Not exactly. People still use the phrase “SSL” informally, but modern secure web access relies on TLS. In everyday usage, “SSL certificate” often refers to a certificate used for HTTPS, even though the underlying secure protocol today is TLS rather than legacy SSL.
Does HTTPS mean a website is completely safe?
No. HTTPS helps protect data in transit and supports server authentication, but it does not guarantee that the website is legitimate, well coded, malware-free, or properly administered. It is a necessary control, not a complete security verdict.
Why do browsers warn about certificate errors?
Browsers issue warnings when they cannot properly validate the server identity or trust chain. Common causes include expired certificates, hostname mismatches, incomplete intermediate certificates, or certificates issued by an untrusted authority.
Can HTTPS be used for device management?
Yes. Many routers, gateways, IP PBX systems, cameras, servers, and industrial devices provide HTTPS-based management interfaces. In those cases, HTTPS helps protect administrator credentials and configuration traffic.
What is HSTS and why is it useful?
HSTS, or HTTP Strict Transport Security, is a policy that tells browsers to access a host only over HTTPS in future visits. It helps reduce downgrade risks and prevents users from bypassing certain certificate warnings after the policy is learned.
Do APIs also need HTTPS?
Yes. APIs often carry tokens, credentials, commands, and business data. Even if an API has application-layer authentication, HTTPS is still important to protect the transport path and reduce interception or tampering risks.
Conclusion
HTTPS secure access is the standard way to protect browser-based and web-enabled communication across modern digital systems. At its core, it means using HTTP over TLS so that websites, portals, APIs, and management interfaces can exchange data more safely across untrusted networks. Its value comes from a combination of encryption, integrity protection, server authentication, and compatibility with modern web security expectations.
In practical terms, HTTPS secure access is no longer limited to large public websites. It is now central to cloud services, enterprise portals, remote device administration, digital transactions, and API-driven architectures. For organizations building or operating web-facing systems, HTTPS is not the whole security strategy, but it is one of the first controls that must be done correctly.