Alarm acknowledgment is the process of confirming that an alarm event has been seen, recognized, and accepted for action by an operator, system user, or responsible team. In simple terms, it tells the system that the alarm is no longer unnoticed. The condition that triggered the alarm may still exist, but the event has been actively recognized rather than left as an unanswered alert. This distinction is very important in environments where many alarms can appear across devices, sites, or control interfaces within a short period of time.
In practical operations, alarm acknowledgment is widely used in industrial control systems, security platforms, building management, transport operations, public safety systems, network monitoring, and integrated communication environments. The purpose is not simply administrative. Acknowledgment creates a visible step between alarm generation and alarm response. It helps operators and teams know whether an event is still unattended, already under review, or being handled by a responsible person.
This makes alarm acknowledgment an important part of operational discipline. In systems where alarms are linked to safety, service continuity, equipment protection, communication incidents, or emergency workflows, it is not enough for the alarm to sound. The platform also needs a mechanism that shows whether the event has actually been noticed and accepted for follow-up. That is where alarm acknowledgment becomes essential.
What Is Alarm Acknowledgment?
Definition and Core Meaning
Alarm acknowledgment refers to the action of confirming receipt and recognition of an alarm after it has been generated by a device, system, or monitoring platform. This confirmation is usually performed by an operator through a control console, software interface, dispatch platform, or supervisory terminal. Once acknowledged, the system marks the alarm as seen or accepted, even if the underlying condition remains active.
The core meaning is operational recognition. An alarm that has not been acknowledged may still be active and unattended. An alarm that has been acknowledged is no longer invisible to the team. This helps establish responsibility and reduces uncertainty around whether the event is being ignored, overlooked, or already under investigation.
In many professional systems, acknowledgment is a separate step from alarm clearance. Acknowledgment means the alarm has been noticed. Clearance usually means the condition has ended or has been reset successfully. This distinction is fundamental to proper alarm management.
Alarm acknowledgment does not mean the problem is solved. It means the problem has been seen and accepted for action.
Why It Matters in Real Operations
In real environments, many alarms may occur close together. Some may be routine, others may be critical, and some may be symptoms of a wider incident. Without acknowledgment logic, operators may struggle to distinguish between alarms that are still unseen and alarms that are already under review. This can create duplication, confusion, or delayed response.
Alarm acknowledgment matters because it creates a controlled response state. It tells other users and systems that the event has entered the response process. This is especially valuable in control rooms, industrial plants, transport facilities, network operations, and communication platforms where more than one person may be monitoring the same event environment.
In that sense, acknowledgment is not only a button press. It is an operational signal that supports teamwork, accountability, and orderly incident handling.
How Alarm Acknowledgment Works
From Alarm Generation to Operator Confirmation
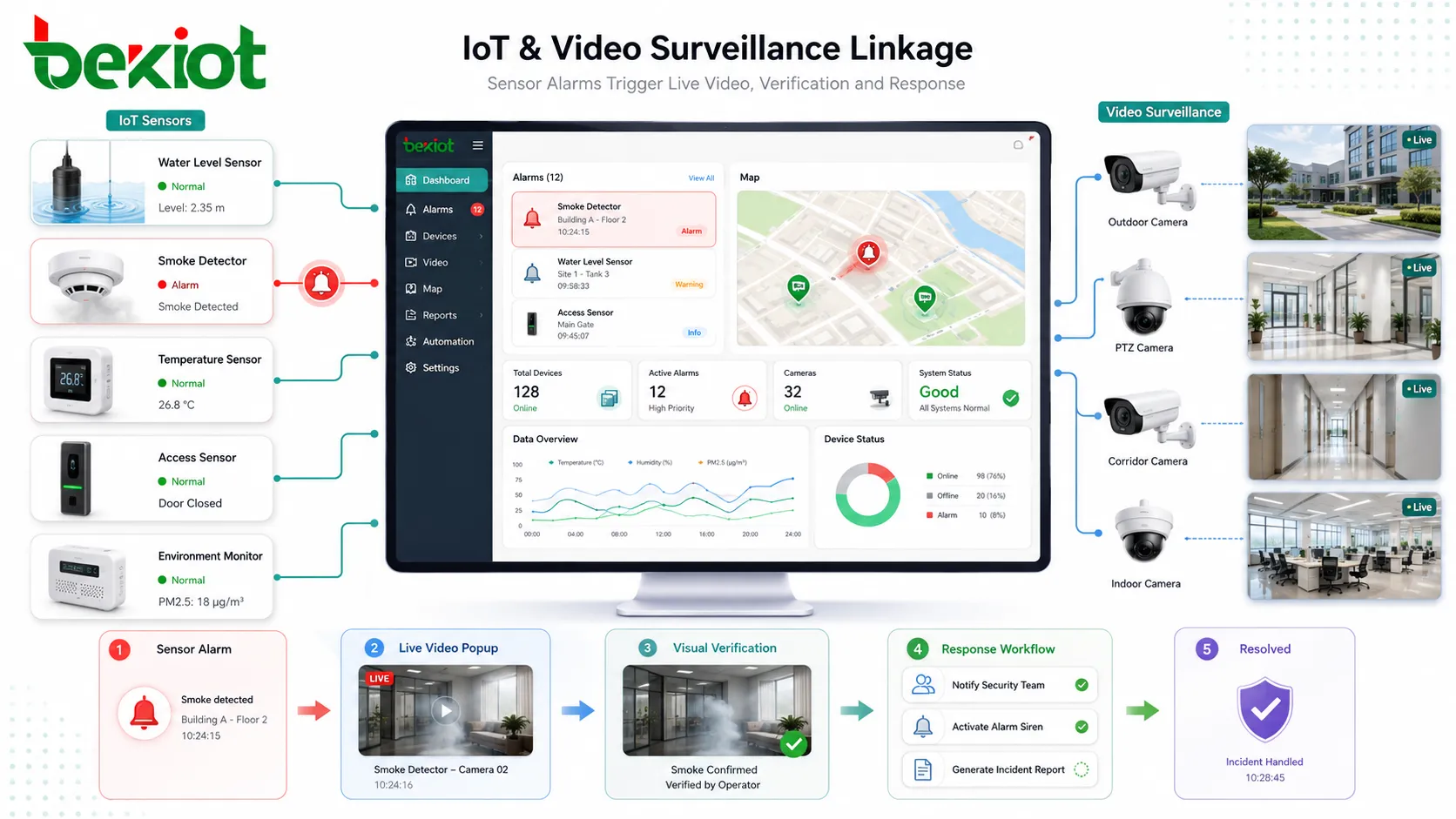
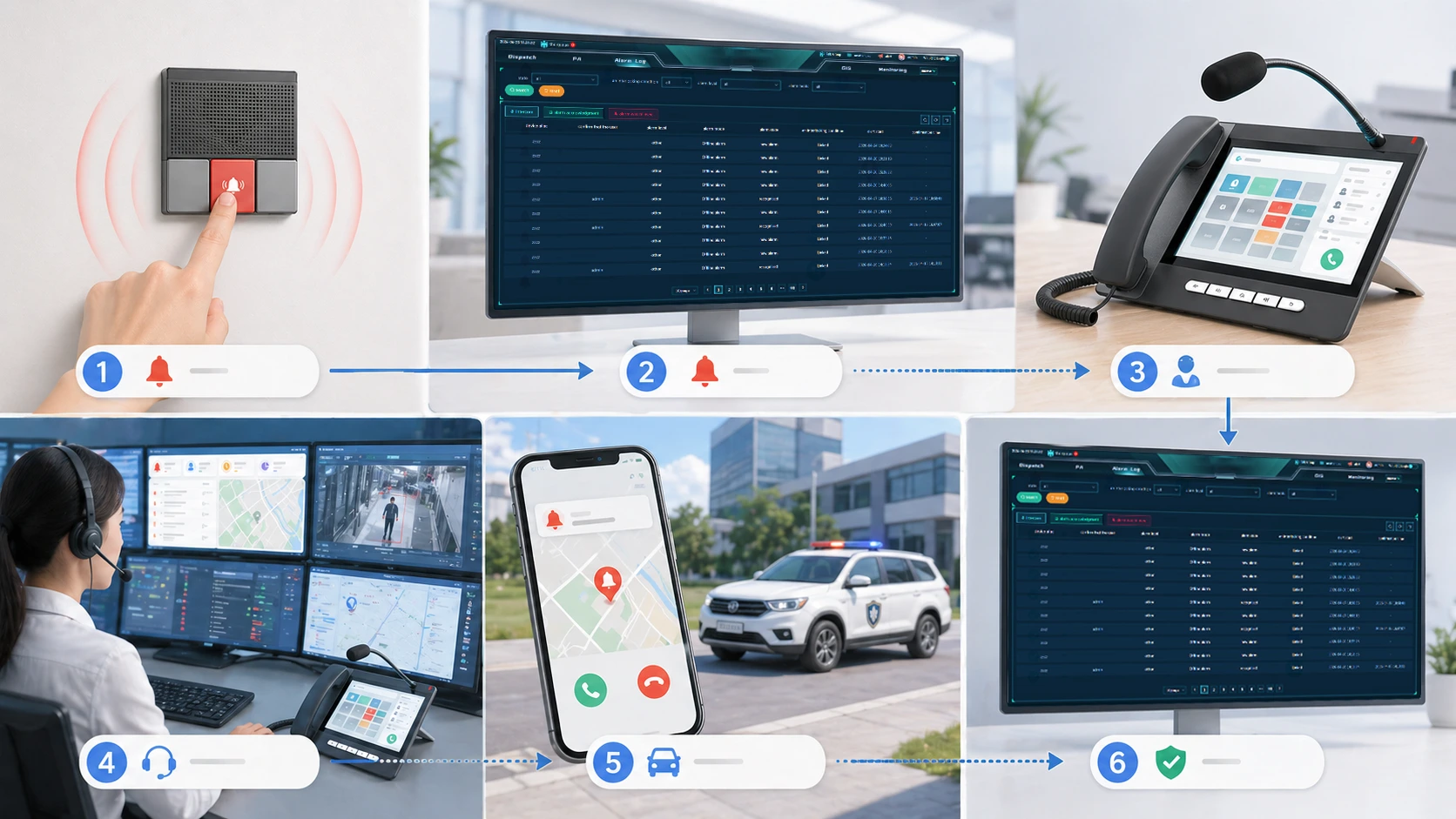
The mechanism usually begins when a monitored condition crosses a defined threshold or a specific event occurs. A system may generate an alarm because of equipment failure, abnormal process value, emergency call activity, communication loss, intrusion event, power issue, network fault, or other operational trigger. Once created, the alarm is displayed to the user through a monitoring or dispatch interface and may also produce sound, flashing indicators, notifications, or escalation actions.
When the responsible operator sees the alarm, that person can acknowledge it through the interface. This action updates the alarm state and records that the event has been noticed. Depending on the system design, the acknowledgment may also log the operator name, timestamp, terminal location, priority status, and related workflow notes.
The system then distinguishes between the original alarm condition and the response state. The underlying issue may still be active, but the platform now knows that the event has entered human awareness and operational handling.
Acknowledgment Versus Reset or Clearance
One of the most important parts of the mechanism is the difference between acknowledgment and clearance. Acknowledgment confirms recognition. Clearance confirms that the alarm condition has ended, has been normalized, or has been deliberately reset according to system logic. In many industrial, security, and dispatch systems, these two actions must remain separate for good reason.
If acknowledgment automatically removed the alarm completely, teams could lose visibility before the real issue is resolved. By separating the two steps, the platform allows operators to say, “We have seen this,” without incorrectly implying, “This problem no longer exists.”
This mechanism improves reliability because it preserves both awareness and technical accuracy during the incident lifecycle.
Acknowledgment is the moment an alarm becomes operationally owned, while clearance is the moment the alarm condition is no longer active or requires no further alarm state.
Main Features of Alarm Acknowledgment
Visible Status Change and Operator Traceability
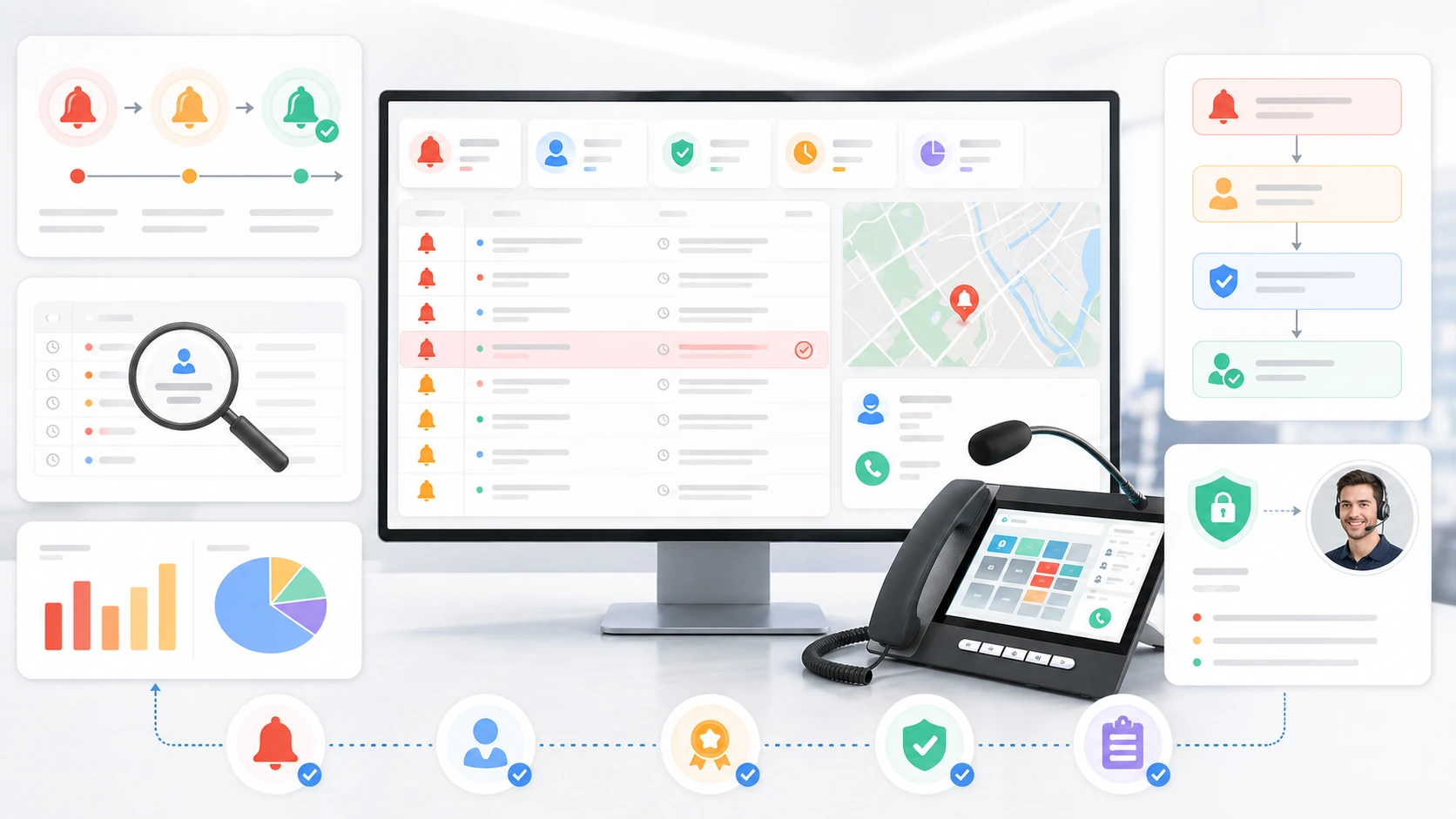
One of the most important features of alarm acknowledgment is status visibility. Once acknowledged, the alarm usually changes appearance in the interface so operators can tell that it has already been seen. This may involve color changes, status text, icon updates, or movement into another workflow column depending on the platform design.
Another major feature is traceability. Many systems record who acknowledged the alarm, when the acknowledgment happened, and what device or terminal was used. This creates useful accountability for operations, reporting, and incident review. In complex environments, this can be extremely helpful because it reduces uncertainty over whether someone has actually taken responsibility for the event.
Together, these features help transform an alarm from a raw alert into a managed operational object within the control process.
Priority Awareness and Workflow Support
Alarm acknowledgment often works together with severity or priority logic. Critical alarms may require immediate acknowledgment, visible escalation, or multiple confirmation steps. Lower-priority events may still need acknowledgment, but with different urgency rules. This helps organizations match response behavior to event importance rather than treating every signal in exactly the same way.
In more advanced systems, acknowledgment also supports workflow logic. An acknowledged alarm may open related panels, link to maintenance tasks, enable incident notes, trigger dispatch actions, or prevent duplicate escalation when the event is already under review. This makes the feature more than just a status marker.
In practical use, alarm acknowledgment often becomes the entry point into broader incident handling.
Benefits of Alarm Acknowledgment
Reduced Confusion and Better Team Coordination
One of the clearest benefits is reduced confusion. In busy operational environments, more than one person may be watching the same alarm field. Without acknowledgment, teams may not know whether an event is still completely unattended or already under review by another operator. This can create duplicated effort or, worse, dangerous assumptions.
Acknowledgment makes the response state visible. Once an alarm has been accepted by someone, the rest of the team can see that the event has moved from “new and unowned” into “noticed and being handled.” This supports clearer coordination, especially in control rooms, dispatch centers, industrial monitoring environments, and large operational teams.
In practice, the benefit is not only visual neatness. It is stronger teamwork under pressure.
Faster and More Disciplined Incident Handling
Alarm acknowledgment also improves response discipline. By creating a formal recognition step, it helps ensure that alarms are not simply heard and forgotten. Operators are encouraged to confirm receipt and begin response in a structured way rather than relying only on informal awareness.
This is particularly useful when alarms trigger larger workflows involving field teams, security personnel, maintenance staff, supervisors, or communication operators. The acknowledgment confirms that the event has entered the response chain and is no longer sitting in an ambiguous state.
That structured handoff can improve both speed and control, especially during busy or multi-event conditions.
Alarm acknowledgment creates order at the moment when an alert first demands attention, which is often where operational clarity matters most.
Additional Operational Benefits
Better Auditability and Incident Review
Another important benefit is better auditability. When acknowledgment is recorded with timestamps and operator identity, organizations can reconstruct how alarm events were handled. This is valuable for training, compliance review, quality improvement, and incident investigation. It helps answer practical questions such as when the event was first seen, who accepted it, and whether response timing matched expectations.
In environments where alarm management affects safety, service continuity, or regulated operations, this type of record can be very important. Even in ordinary enterprise systems, acknowledgment history can help improve accountability and reveal workflow weaknesses over time.
This means alarm acknowledgment contributes not only to live operations, but also to long-term organizational learning.
Lower Risk of Alarm Neglect
Alarm acknowledgment also helps reduce the risk that important events remain unnoticed or psychologically ignored within a busy alarm environment. When platforms distinguish clearly between unacknowledged and acknowledged alarms, truly unattended events stand out more visibly. This makes it easier for teams to recognize where attention is still missing.
In practical terms, that can support better alarm discipline and reduce the chance that significant events disappear into a crowded screen of alerts. Acknowledgment does not eliminate alarm overload by itself, but it does make unattended alarms easier to identify and manage.
This is especially useful in high-density monitoring systems where the risk of alarm fatigue is real.
Applications of Alarm Acknowledgment
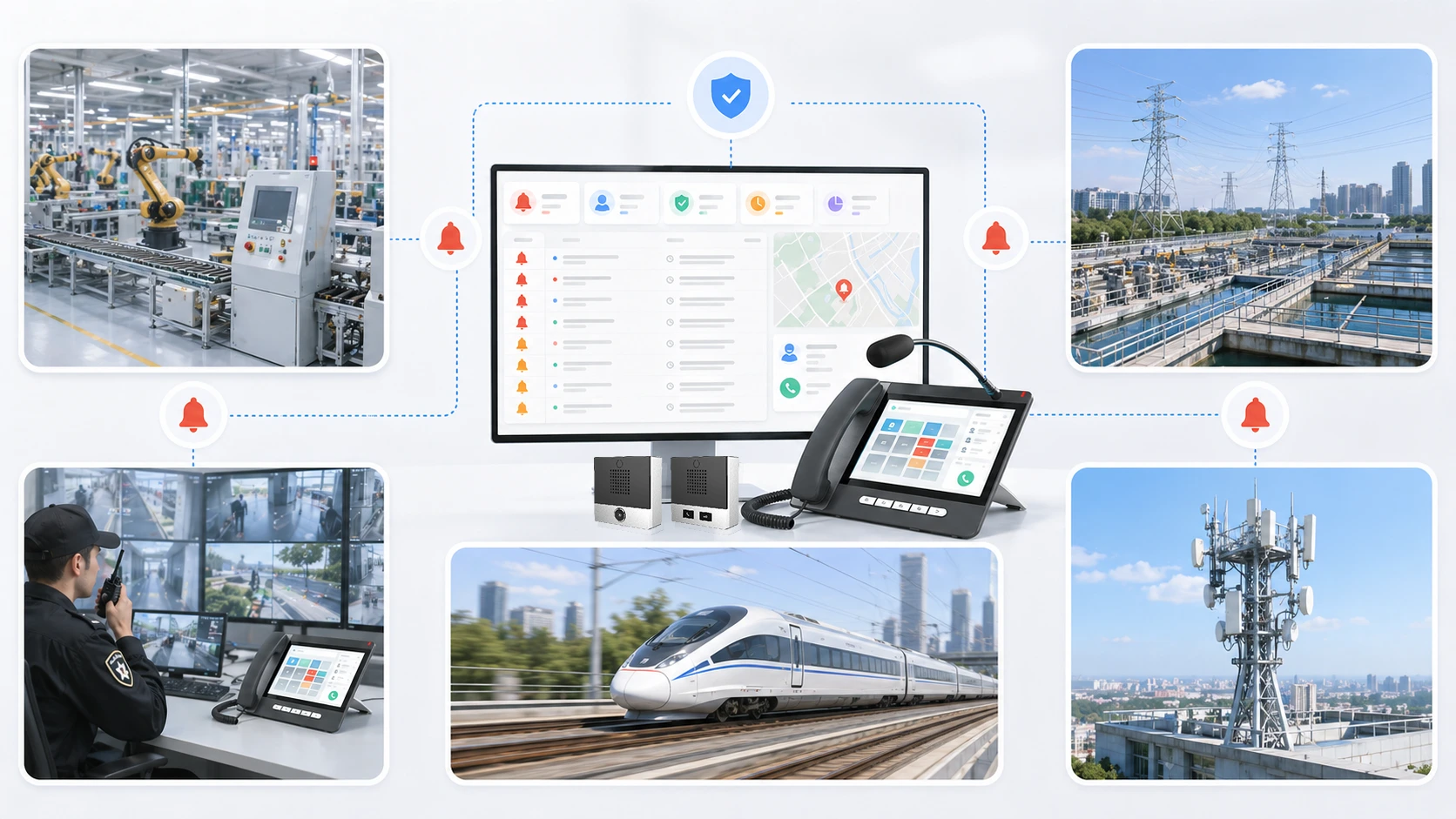
Industrial Control, Utilities, and Facility Monitoring
Alarm acknowledgment is widely used in industrial control systems, utilities, process plants, substations, and facility monitoring environments. In these systems, alarms may indicate abnormal process values, equipment trips, environmental warnings, communication faults, or power events. Operators need a clear way to confirm that the alert has been seen before technical resolution occurs.
These environments often rely on acknowledgment because operational teams work in shifts, incidents may continue for extended periods, and the distinction between “active” and “unnoticed” must remain clear. The feature therefore supports both technical control and shift-based accountability.
In practice, alarm acknowledgment becomes part of how the site maintains operational awareness and response discipline.
Security, Transport, and Communication Platforms
Security systems, transport control environments, and communication platforms also use alarm acknowledgment extensively. A security alert, emergency call event, network loss alarm, dispatch exception, or site equipment fault may all require acknowledgment before further actions unfold. This helps ensure that the event is visible not only as a system signal, but as a managed response item.
In transport and command environments, the same logic applies. Operators may need to acknowledge platform alarms, roadside incidents, tunnel communication faults, emergency help-point activity, or service interruptions before assigning field or control actions.
In these cases, acknowledgment supports clarity between detection and coordinated operational response.
Alarm Acknowledgment in Communication Projects
Role in Intercom, Paging, and Dispatch Systems
In communication projects, alarm acknowledgment is especially relevant where alarm events are linked to intercom systems, paging triggers, help points, emergency communication terminals, or dispatch workflows. A call-for-help event, communication fault, or alarm-linked broadcast trigger may need acknowledgment so operators know the event has entered response control.
This is important because communication incidents often involve both technical and human response layers. The system may detect the event automatically, but the operational value increases only when someone confirms that the event has been seen and accepted for handling. In dispatch systems, acknowledgment therefore helps bridge automatic alerting and operator-led coordination.
That makes the feature useful not only in process control, but also in communication-centered incident management.
Case Study Analysis
For example:Becke Telcom Alarm System.Within the integrated communication architecture of Becke Telcom’s specialized telecommunications projects, the Alarm Acknowledgment feature facilitates deep-level linkage and collaboration among SIP intercoms, industrial telephones, emergency call points, public address systems, and the visual dispatch platform. On-site alarm events are no longer confined to mere single-device fault notifications; instead, they are comprehensively integrated into the entire operational workflow—encompassing on-site communication dispatch, operator emergency response, regional situational awareness, and the tiered escalation of incidents.
Leveraging a meticulously designed alarm acknowledgment mechanism, Becke Telcom’s communication solutions enable standardized and regulated alarm management. This system clearly records the specific triggers for each event and the response status of the designated personnel, while providing a complete audit trail covering the entire operational process—from initial alarm detection and information dissemination to on-site resolution. This capability is particularly well-suited for critical environments such as industrial parks, manufacturing complexes, tunnel projects, transportation hubs, and municipal utility sites, where it serves to establish a robust foundation for orderly communication and emergency dispatch operations.
Alarm Acknowledgment has been deeply embedded into the overall design of Becke Telcom’s solutions, creating a closed-loop synergy between the visual presentation of alarms and the corresponding emergency communication response. This integration delivers efficient, controllable, and fully traceable intelligent alarm dispatch capabilities across a wide spectrum of critical communication scenarios.
Maintenance Tips for Alarm Acknowledgment Systems
Keep Alarm Priorities and Acknowledgment Rules Clear
One of the most important maintenance tasks is ensuring that acknowledgment rules remain aligned with real operational priorities. If the system asks operators to acknowledge too many insignificant events in the same way it treats critical alarms, the acknowledgment process may lose meaning. Over time, users may respond mechanically instead of thoughtfully.
This means alarm classes, severity logic, and operator workflows should be reviewed regularly. Critical alarms may require stronger attention, escalation linkage, or supervisor visibility. Lower-level events may still need acknowledgment, but not necessarily in the same way. Clear prioritization helps preserve the operational value of the acknowledgment action.
In practical terms, good alarm acknowledgment depends on good alarm design overall.
Review Logs, Training, and Response Patterns
Maintenance should also include review of acknowledgment logs and operator behavior. Are alarms being acknowledged too slowly? Are events being acknowledged without proper follow-up? Are the same alarm groups being repeatedly mishandled? These patterns can reveal weaknesses in training, interface design, or workload distribution.
Teams should also be trained to understand what acknowledgment means in the local operating context. If users treat it as alarm deletion rather than alarm acceptance, the system may still work technically while failing operationally. Clear training helps preserve the integrity of the mechanism.
Alarm acknowledgment is most effective when it is supported by good process discipline as well as working software.
A good acknowledgment system depends not only on the interface, but on whether operators understand that acknowledgment is a response commitment, not a visual cleanup action.
Best Practices for Alarm Acknowledgment
Separate Recognition From Resolution
One of the best practices is to keep acknowledgment separate from alarm clearance or reset. This protects operational accuracy by ensuring that recognition of the event does not falsely suggest that the problem has ended. The team can acknowledge the alarm quickly while still investigating and resolving the underlying issue properly.
This separation is especially important in industrial, security, and communication systems where conditions may remain active after the first response step. Acknowledgment should improve visibility, not hide ongoing risk.
In practical design terms, this helps preserve both awareness and accountability across the full event lifecycle.
Make Status Visible Across the Team
Another best practice is to make acknowledgment state visible to all relevant users. If only one operator can see that the alarm has been acknowledged, the coordination benefit is limited. Good platforms show the status clearly across the team so others know the event has already entered response handling.
This is especially useful in control rooms, shift operations, and multi-user monitoring environments where several people may watch the same system. Shared visibility helps prevent duplication and improves confidence that important alarms are not still unattended.
Acknowledgment is most useful when it creates shared operational clarity rather than private status change for one user alone.
Conclusion
Alarm acknowledgment is the mechanism that confirms an alarm has been seen and accepted for action, even if the underlying condition still exists. Its value lies in transforming raw alerts into visible, managed response events instead of leaving them in an uncertain or unattended state.
It improves coordination, reduces confusion, strengthens incident discipline, and supports better accountability across industrial systems, security platforms, facility monitoring, transport operations, and communication environments. In more advanced deployments, it also becomes an important bridge between automated detection and human-led response.
For organizations designing reliable alarm and communication workflows, alarm acknowledgment is not just a minor interface feature. It is a practical control that helps ensure alarms are not only generated, but truly noticed and operationally owned.
FAQ
What is alarm acknowledgment in simple terms?
In simple terms, alarm acknowledgment means a person or system confirms that an alarm has been seen and accepted for action. It shows the event is no longer unnoticed.
It does not automatically mean the problem has been fixed.
What is the difference between alarm acknowledgment and alarm clearance?
Alarm acknowledgment means the alarm has been recognized by an operator or responsible user. Alarm clearance usually means the underlying condition has ended or the event has been reset properly.
Acknowledgment and clearance are different steps and should usually remain separate.
Where is alarm acknowledgment commonly used?
Alarm acknowledgment is commonly used in industrial control systems, utilities, security platforms, transport operations, facility monitoring, dispatch systems, communication platforms, and emergency response environments.
It is especially valuable where alarms must be clearly tracked from detection to human response.