Redundancy refers to the deliberate duplication of critical components, functions, links, or resources in a system so that service can continue even if one part fails. In practical engineering and operational terms, redundancy is not waste. It is a reliability strategy. The goal is to reduce single points of failure and improve the ability of a system to remain available during faults, maintenance events, overload conditions, or unexpected disruptions.
The concept appears across many technical and operational fields. In networking, redundancy may mean dual uplinks, backup switches, or multiple transmission paths. In telephony and unified communications, it may involve redundant SIP servers, standby IP PBX platforms, duplicated gateways, or backup call routing logic. In power systems, it can include dual power supplies, battery backup, and redundant power feeds. In industrial environments, redundancy often extends further to include duplicated controllers, communication paths, field devices, and failover servers that support high-availability operations.
Although redundancy is often discussed in the context of infrastructure and critical systems, the underlying idea is simple. A system becomes fragile when one failure can stop the whole service. Redundancy reduces that fragility by ensuring that an alternative path, device, or service instance is already prepared to take over. For this reason, redundancy is one of the most important design principles in communication networks, security systems, automation platforms, public safety systems, and enterprise IT architecture.
Redundancy improves service continuity by adding backup resources and reducing single points of failure.
What Redundancy Means in Practice
More Than a Simple Backup
Many people use the words redundancy and backup as if they mean the same thing, but in real system design they are related rather than identical. A backup is often a reserve copy or standby resource that may be used after a failure, while redundancy usually implies that multiple resources are already built into the live system architecture. In other words, redundancy is not only about recovery after something goes wrong. It is about designing the system so that it can continue operating with minimal interruption when something goes wrong.
For example, a backup configuration file stored offline is useful, but it does not create real-time service continuity. By contrast, a redundant server pair, a secondary network path, or a second power supply can support continuity while the system is still running. This distinction is especially important in environments where service interruptions are costly or dangerous, such as hospitals, control rooms, transport hubs, industrial plants, emergency communication systems, and large enterprise networks.
That is why redundancy is often treated as part of availability engineering rather than only part of disaster recovery. It addresses the question of how the system behaves during a fault, not just how it can be rebuilt after failure has already caused downtime.
Reducing Single Points of Failure
The most common reason for using redundancy is to eliminate or reduce single points of failure. A single point of failure is any component whose failure can bring down the larger system. This may be a network switch, a power module, a server, a storage device, a gateway, a controller, or even a cable path. If that element fails and no alternative exists, the service stops.
Redundancy changes that risk model. Instead of depending on one critical element, the system is designed so that another component, route, or instance can continue the task. In some designs, the spare resource remains idle until needed. In others, both resources are active and share the load. Either way, the objective is to keep the service available even when a fault occurs.
This is why redundancy is so valuable in modern communication systems. Voice, data, control, and alarm functions increasingly depend on interconnected digital infrastructure. When one failure affects multiple services at once, the operational impact can be much larger than in older isolated systems. Redundancy helps contain that risk.
Redundancy is the engineering decision to assume that failures will happen and to design the system so that those failures do not become service collapse.
How Redundancy Works
Standby and Active-Active Models
Redundancy can be implemented in several ways, but two common models are active-standby and active-active. In an active-standby design, the primary resource handles the service under normal conditions while the secondary resource waits in reserve. If the primary fails, the secondary takes over. This approach is common in servers, controllers, gateways, power modules, and communication nodes where simplified failover behavior is desirable.
In an active-active model, multiple resources are active at the same time. They may share traffic, process requests in parallel, or provide mutual continuity if one instance fails. This design can improve both availability and capacity, but it often requires more careful synchronization, state handling, and traffic management. In networking and data services, active-active approaches are especially common where load sharing and continuous responsiveness are both important.
The best choice depends on the application. Active-standby is often simpler to control and verify, while active-active may deliver stronger performance and smoother continuity in larger systems. Both approaches are forms of redundancy, but they differ in operational behavior and design complexity.
Failover, Switchover, and Recovery Logic
Redundancy becomes useful only when the system knows how to react to faults. This is where failover logic matters. A redundant design usually includes health monitoring, heartbeat signals, synchronization mechanisms, role definitions, and switchover rules. When the system detects that a resource is no longer functioning correctly, it initiates a transition so the alternative resource can continue providing service.
That transition may be automatic or manual depending on the environment. In critical communications, automatic failover is often preferred because delay can disrupt voice traffic or response operations. In some industrial or regulated settings, a supervised or semi-manual switchover may be used to maintain control over system state and process safety. In either case, the effectiveness of redundancy depends not just on having extra hardware or software, but on managing the transition correctly.
Recovery also matters after failover. Once the failed component is repaired, the system must decide whether to return service to the original resource immediately, wait for operator approval, or keep the backup in control until a scheduled maintenance window. These policy choices affect stability and should be planned rather than improvised.
Synchronization and State Awareness
In many redundant systems, the secondary resource must be ready to take over without losing critical context. That means configuration data, session information, call state, routing tables, user data, alarms, or application status may need to be synchronized between primary and secondary components. Without synchronization, failover may preserve infrastructure availability but still interrupt the service experience in a major way.
This is especially important in voice and communication systems. A redundant SIP platform, dispatch server, or IP PBX may need synchronized user profiles, extension data, route policies, and registration logic. In storage and virtualization environments, synchronized state helps prevent data inconsistency. In industrial control systems, synchronized logic is essential to keep automation behavior predictable during changeover.
Because of this, redundancy is not only about physical duplication. It is also about informational continuity. A standby server that exists but is not synchronized may still leave the organization vulnerable to service disruption when it takes over.
Key Features of Redundancy
High Availability Support
The most widely recognized feature of redundancy is improved availability. A redundant design helps services remain accessible even when hardware, software, or connectivity problems occur. Instead of treating uptime as a matter of luck, redundancy makes availability part of the architecture itself. This is especially valuable in systems that support live communication, operations coordination, alarms, security, or customer-facing interaction.
In real deployments, high availability is not only about whether the system is technically online. It is also about whether users can continue their work with minimal disruption. A communication system that drops all active registrations or becomes unreachable during a single server fault may not meet operational expectations even if it can be restarted quickly. Redundancy reduces that exposure by preparing continuity paths in advance.
This is why high availability design is often inseparable from redundancy planning. Where uptime matters, redundancy is usually one of the primary tools used to achieve it.
Fault Tolerance and Service Continuity
Redundancy is closely associated with fault tolerance, but the two ideas are not exactly the same. Fault tolerance refers to the system’s ability to continue functioning correctly despite faults. Redundancy is one of the mechanisms that helps achieve that outcome. By duplicating critical resources, the system gains tolerance for failure in areas that would otherwise cause immediate service interruption.
In communication and infrastructure systems, this means users can often continue making calls, accessing services, or exchanging data even if one node, link, or power source is lost. In industrial environments, it may mean that monitoring, broadcasting, intercom, or control operations continue without a dangerous blind spot. In enterprise IT, it may allow applications and user sessions to remain available while faults are isolated and repaired.
Service continuity is the practical result users care about. They may not see the redundancy logic directly, but they experience the system as dependable and resilient under stress.
Flexible Maintenance and Operational Resilience
Another important feature of redundancy is that it supports maintenance without requiring full service interruption. If a platform has redundant servers, switches, links, or power supplies, technicians may be able to service one part while the other continues carrying the workload. This improves lifecycle manageability and reduces the cost of maintenance windows.
Redundancy also supports operational resilience during partial degradation. Not every problem is a total failure. Sometimes the issue is overload, intermittent instability, planned upgrades, or temporary environmental disruption. A redundant design provides options for rerouting, isolating, and stabilizing services before a small issue becomes a major outage.
That resilience becomes increasingly important as organizations rely on always-on digital communication. The system must survive not only rare disasters, but also routine faults and maintenance realities.

Redundancy supports high availability, fault tolerance, and more flexible maintenance in communication and infrastructure systems.
Common Types of Redundancy
Network Redundancy
Network redundancy is one of the most common forms. It may include multiple uplinks, redundant switches, dual routers, ring topologies, mesh links, or alternative WAN paths. The purpose is to ensure that traffic can still move if one connection or device fails. In business and industrial networks, this is essential because a network outage can affect voice, video, alarms, control traffic, and business applications at the same time.
In real projects, network redundancy is often combined with spanning protocols, routing failover, fast recovery mechanisms, VLAN design, and QoS planning. The network should not only have extra links, but also know how to use them without causing loops, instability, or unpredictable switching behavior. This is especially important for VoIP and SIP traffic, where delay and loss can degrade service quickly.
As communication systems expand across factories, campuses, transport sites, and utility environments, network redundancy becomes a foundational requirement rather than an optional enhancement.
Server and Application Redundancy
Server redundancy is used when applications, control logic, or communication services must remain available despite hardware or software failure. This may involve clustered servers, virtualized failover environments, mirrored application nodes, or standby service instances. In SIP and IP communication platforms, redundancy may cover call control servers, provisioning systems, voicemail platforms, dispatch servers, and management applications.
Application redundancy is especially important where users depend on central services for registration, authentication, routing, or coordination. If a single communication server fails, hundreds or thousands of endpoints may be affected. Redundancy reduces that concentration of risk by ensuring the service can continue from another node.
Successful server redundancy requires more than installing a second machine. It also depends on synchronization, health checks, database handling, and a clearly defined failover sequence that fits the application.
Power Redundancy
Many outages begin not with software failure but with power disruption. Power redundancy addresses this risk by providing more than one energy source or delivery path. Common examples include dual power supplies, independent power feeds, UPS systems, battery backup, generator integration, and power module duplication inside network or communication equipment.
In communication systems, power redundancy is critical because even a well-designed network and server architecture becomes unavailable if power is lost at a central node or field endpoint. This is especially important in emergency telephony, paging systems, transport communication, industrial intercom, and control room environments where service may be needed most during infrastructure stress.
For that reason, power redundancy is often treated as inseparable from communication redundancy. The network path and the power path must both be resilient, otherwise the overall availability target cannot be achieved.
Storage and Data Redundancy
Data also needs protection. Storage redundancy may involve mirrored disks, RAID configurations, replicated databases, synchronized storage nodes, and remote data copies. The purpose is to prevent loss of information or service interruption when a storage device fails. In enterprise systems, this supports application continuity. In communication platforms, it may protect user records, logs, voicemail, configuration data, routing rules, and event history.
However, storage redundancy should not be confused with complete data protection. Mirroring protects against some types of hardware failure, but it does not automatically solve corruption, accidental deletion, or application-level errors. For this reason, organizations usually combine redundancy with backup and recovery planning rather than treating one as a substitute for the other.
This illustrates an important point: redundancy improves continuity, but it works best when combined with broader resilience strategy.
Applications of Redundancy
Communication Systems and IP Telephony
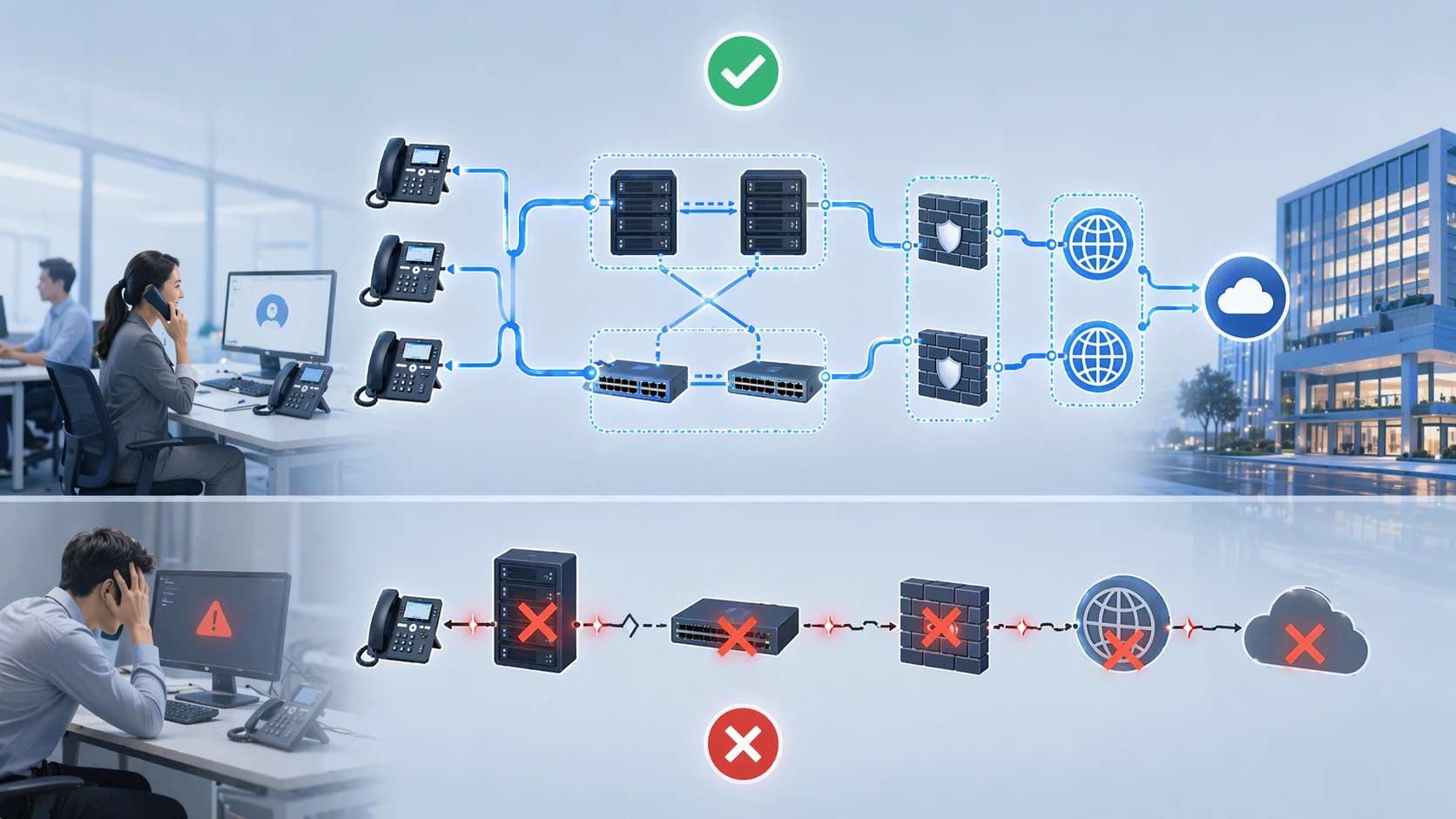
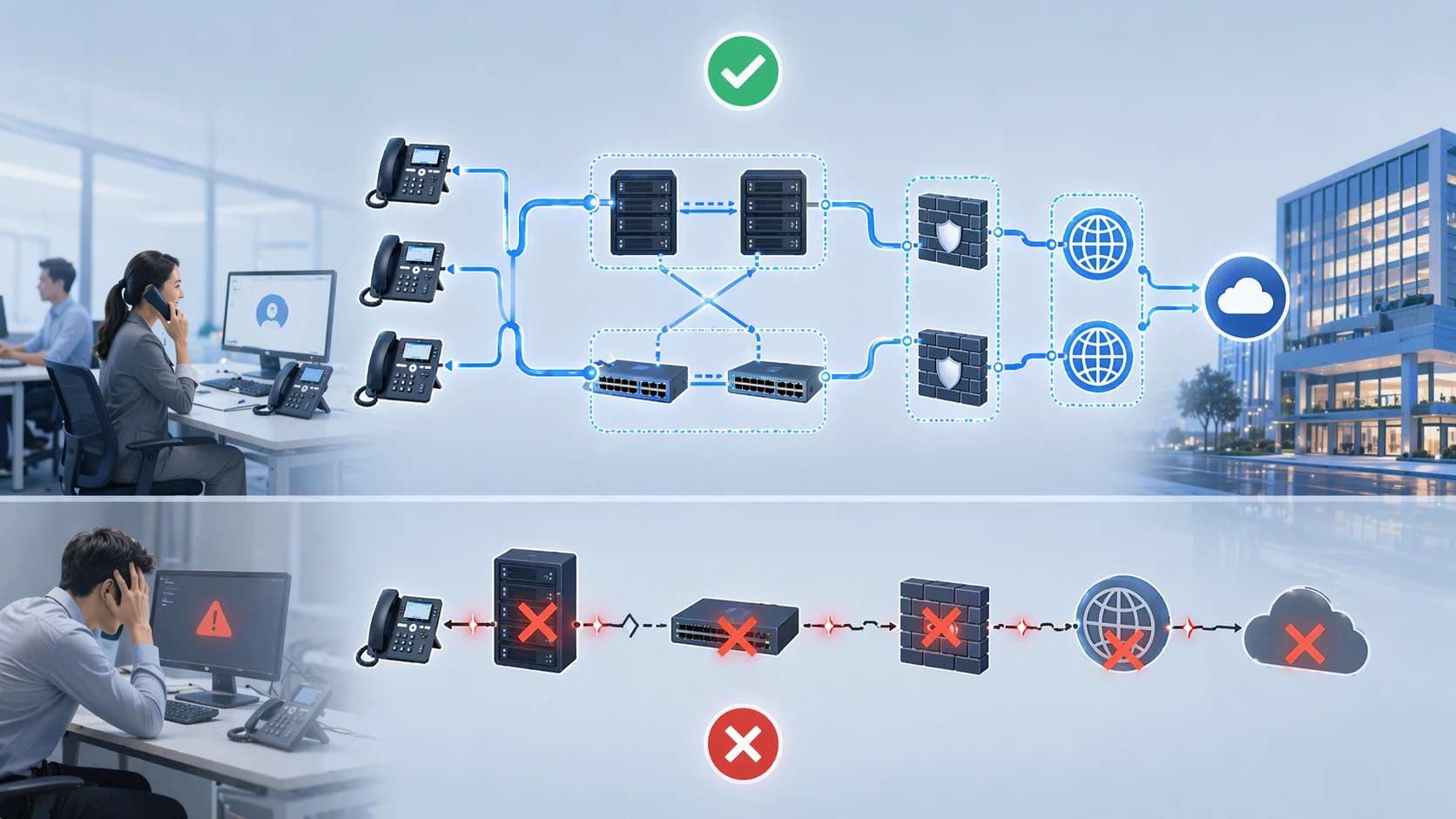
Redundancy is widely used in communication platforms because voice services are expected to be continuously available. In SIP and IP telephony environments, redundancy may involve duplicated SIP servers, backup IP PBX nodes, secondary session border elements, redundant gateways, and alternative WAN connectivity. These designs help ensure that calls can still be processed even if one node or path fails.
In practical terms, this matters for offices, campuses, hospitals, industrial sites, transport facilities, and emergency coordination centers. A phone system may be central to daily operations, customer interaction, and incident response. If the main server or network path fails without redundancy, the communication impact can be immediate and widespread.
This is why modern business telephony increasingly treats redundancy as an expected architectural feature rather than a premium extra. As systems become more integrated with paging, intercom, alarms, video, and dispatch, the value of communication continuity becomes even higher.
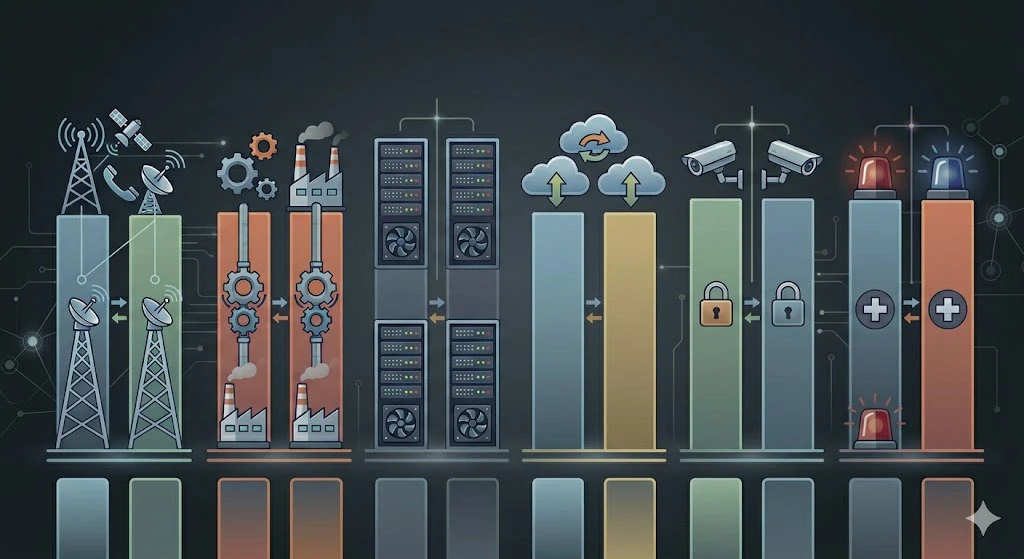
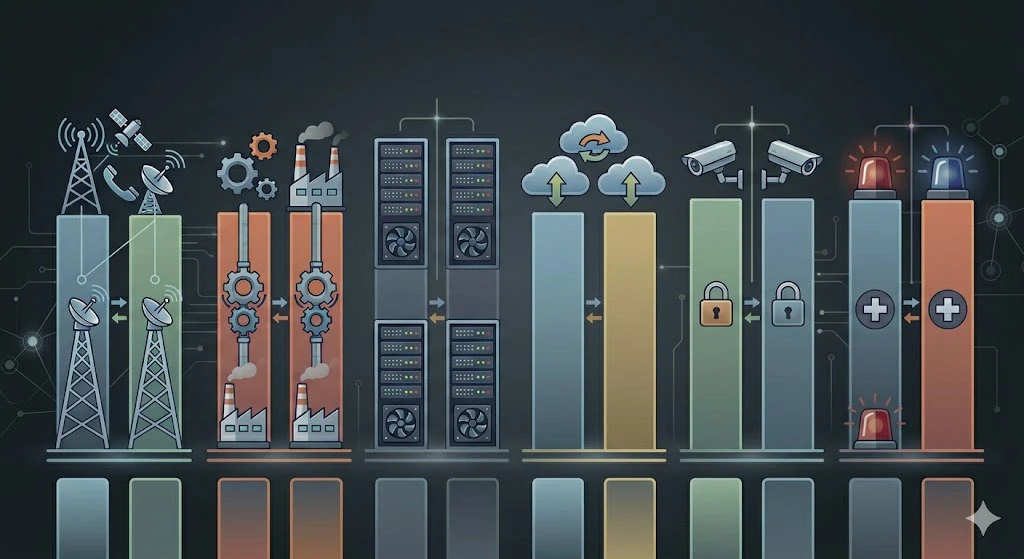
Industrial Control and Critical Infrastructure
Industrial and critical infrastructure environments rely heavily on redundancy because service interruption may affect not only productivity but also safety. Power plants, refineries, tunnels, metro systems, water facilities, utility corridors, and manufacturing sites often use redundant communication links, control servers, network paths, and power designs to reduce operational risk.
In such environments, redundancy may support SCADA communication, industrial telephony, PAGA systems, alarm broadcasting, dispatch consoles, field intercom, and central monitoring platforms. The objective is to preserve visibility and control even during equipment faults or infrastructure stress. This is especially important where operators need continuous awareness of plant status and the ability to communicate with field personnel.
Because the cost of failure can be high, redundancy in these sectors is usually planned more deliberately and tested more rigorously than in ordinary office environments.
Data Centers, Enterprise IT, and Cloud Services
In enterprise IT and data center environments, redundancy supports application availability, service continuity, and business resilience. Organizations use redundant compute nodes, network fabrics, storage systems, cooling paths, and power infrastructure to keep digital services accessible. Even where cloud services are involved, redundancy remains important because the architecture still depends on resilient connectivity, platform design, and service distribution.
For users, this may appear as a website that remains online, a communication platform that keeps working, or a remote collaboration service that survives localized faults. Behind that experience is often a carefully layered redundancy model that distributes risk across hardware, software, and connectivity layers.
As business operations become more digital, redundancy becomes less of a specialist topic and more of a baseline requirement for dependable service delivery.
Security, Safety, and Emergency Operations
Security and emergency systems are another major application area. Video surveillance backbones, access control servers, emergency call platforms, public address systems, dispatch solutions, and alarm distribution networks often require redundancy because they must remain available during abnormal conditions. In many cases, these are the exact moments when the systems are needed most.
For example, an emergency call point network may require redundant communication routing and backup power. A control room may need duplicated servers and alternative voice paths. A public safety broadcast system may require redundant amplifiers, network switches, or core management nodes. Without redundancy, the system may fail precisely when its function becomes critical.
This is why redundancy is often treated as a core design principle in safety-related communication and monitoring architecture.
Redundancy is widely used in telephony, industrial systems, enterprise IT, and safety-critical communication environments.
The value of redundancy becomes most visible when the unexpected happens and the system keeps working anyway.
Design Considerations for Redundant Systems
Complexity, Cost, and Testing
Redundancy adds resilience, but it also adds complexity. More devices, more links, more logic, and more synchronization requirements can increase the design burden. If implemented poorly, a redundant system can become difficult to manage or may fail unpredictably during switchover. For this reason, redundancy should be planned with clear architecture, controlled scope, and realistic operational procedures.
Cost is another factor. Redundant components increase hardware, licensing, integration, and maintenance requirements. However, the decision should be based on risk and service importance rather than on hardware cost alone. In many environments, the cost of downtime is far greater than the cost of building redundancy correctly.
Testing is essential. A redundant design that is never tested may create false confidence. Organizations should verify failover behavior, timing, state preservation, alarm handling, and recovery procedures under controlled conditions.
Match Redundancy to Real Business Risk
Not every component needs the same level of redundancy. Effective design begins with identifying which services are truly critical and what level of interruption is acceptable. A control room voice server may justify full redundancy, while a nonessential reporting tool may not. A backbone switch may require duplicated uplinks, while a low-impact local printer does not need the same attention.
This risk-based approach helps organizations apply redundancy where it delivers the most value. It also prevents overdesign, where complexity is increased without meaningful operational benefit. The goal is not to duplicate everything blindly. The goal is to protect the parts of the system whose failure would have disproportionate consequences.
Good redundancy planning is therefore strategic. It aligns technical architecture with operational priorities.
Conclusion
Why Redundancy Matters
Redundancy matters because modern systems are too important to depend entirely on one path, one node, or one power source. Whether the environment is an office phone system, an industrial communication platform, a control network, or a cloud-based enterprise service, the risk of single-point failure can disrupt operations, reduce safety, and damage service quality. Redundancy reduces that risk by preparing continuity in advance.
Its practical value lies in improved availability, stronger fault tolerance, better maintenance flexibility, and more dependable service during abnormal events. At the same time, redundancy is not just a matter of adding extra hardware. It requires good failover logic, synchronization, testing, and architecture discipline. The most effective redundant systems are those designed around real operational needs rather than abstract technical ambition.
As organizations continue to rely on always-on communication and digital infrastructure, redundancy remains one of the most important building blocks of resilient system design.
FAQ
Is redundancy the same as backup?
No. Backup usually refers to a reserve copy or recovery resource, while redundancy typically means duplicate live resources are built into the system to keep service running during a fault.
What is the main purpose of redundancy?
The main purpose is to reduce single points of failure and improve service continuity when equipment, links, software, or power sources fail.
Where is redundancy commonly used?
It is commonly used in networks, SIP and IP telephony systems, industrial control environments, data centers, security platforms, and emergency communication systems.
Does redundancy guarantee zero downtime?
Not always. Redundancy can greatly reduce downtime, but the real result depends on architecture quality, failover design, synchronization, and testing.